Summary:
I have stumbled across multiple “ad servers” which check for versions of Flash. I was playing around with one and was getting redirect to random sites. After a while I was redirected to Rig EK. Bunitu was dropped by Rig which was a nice change from the usual Cerber.
I believe these “ad servers” might be great for EK hunting. I have already found Sundown EK in this manner.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on the PseudoDarkleech campaign and its history:
http://researchcenter.paloaltonetworks.com/2016/12/unit42-campaign-evolution-pseudo-darkleech-2016/
- Article on Bunitu Trojan:
https://blog.malwarebytes.com/threat-analysis/2015/07/revisiting-the-bunitu-trojan/
Downloads
- rigbunitu-150217-> Contains pcapng and payload in password protected zip.
Notable Details:
- 206.54.163.4 – onclickads[.]net – Flash version detector
- 206.54.163.50 – onclkds[.]com – 302 redirect
- 104.197.85.202 – adexchangeprediction[.]com – 302 redirect
- 78.46.232.211 – holdem-pokers.info – iframe redirect
- 88.198.220.112 – poks122[.]pw – Compromised Site iframe redirect
- 185.159.130.122 – old.thebestdallasdentists[.]com – Rig EK
- 245.147.26.100 – plastic.firgo6slike.net – DNS request from Bunitu
- Payload was rad73363.tmp.exe -> VirusTotal
Details of infection chain:
(click to enlarge!)
Full Details:
- A malvertising URL contains a Flash version detector.
- Two further 302 redirects.
- iframe redirect to compromised website.
- iframe to Rig EK.
- old.thebestdallasdentists[.]com -> Pre-Landing -> Landing Page -> Flash -> Payload
- Dropped payload “rad73363.tmp.exe”.
-
SHA256: fa092bfd24a1255d5e870b447cfc229e3bc6b0dd3f59ade7fa7369aff45b7a29 File name: rad73363.tmp.exe Detection ratio: 10 / 58 - This was identified as Bunitu Trojan.
- Bunitu opens random ports by changing firewall settings and allows the host to become a remote proxy.
- Bunitu uses a DLL called vsgliig.dll.
- ETPRO TROJAN Win32.Bunitu DNS Lookup (A Network Trojan was Detected) [2824943]
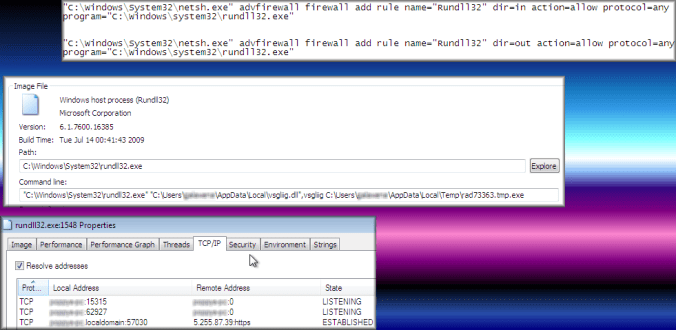
Bunitu opens ports by changing firewall rules.
