Summary:
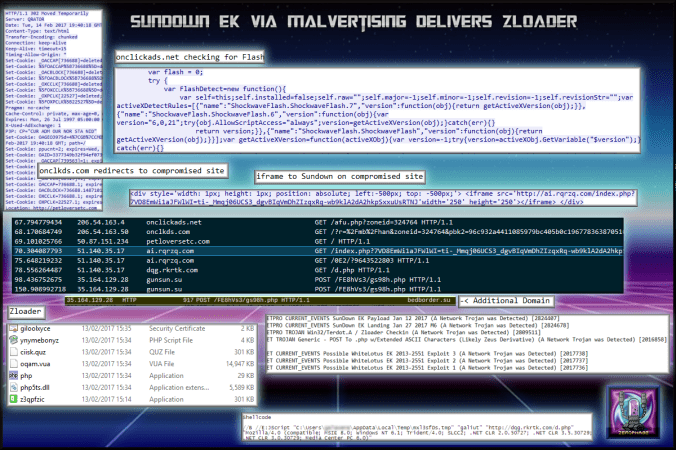
I have finally found Sundown EK without having someone give it to me or borrowed from another researcher. I actually found this from alerts of Magnitude EK and it is quite possible the malvertising site may actually lead to other EK’s. Alas, I was sent to Sundown EK and not Magnitude but this could be an indication that Sundown is using the same mechanisms to get visitors as Magnitude is known for (ads).
This version of Sundown did not use stenography and seemed relatively straight forward. A landing page, one Flash exploit and then a payload. The payload was Zloader which I have seen before being dropped by Sundown.
Anyway the files and pcap are available for download. Perhaps someone can figure out why I saw White Lotus EK exploits ET signatures. I hope the new IOC’s will be of use to the community.
Background Information on Sundown EK:
Sundown EK has changed so much over the past few months that I’m not sure any article can cover what it is today. Sundown is known to use parts of other exploit kits. Recently however it was reported that Sundown uses stenography however I did not see this occur in this sample.
Downloads
- 140217-sundownzloader-> Contains pcapng and payload in password protected zip.
Notable Details:
- 206.54.163.4 – onclickads[.]net – Malvertising
- 206.54.163.50 – onclkds[.]com – Malvertising
- 50.87.151.234 – petloversetc[.]com – Compromised Website
- 51.140.35.17 – ai.rqrzq[.]com – Sundown Landing Page
- 51.140.35.17 – dqg.rkrtk[.]com – Sundown Payload download
- 31.164.129.28 – gunsun[.]su – Zloader
- 31.164.129.28 – bedborder[.]su – Zloader
- Payload was z3qpfzic.exe -> VirusTotal
Details of infection chain:
(click to enlarge!)
Full Details:
- A malvertising URL searches for old versions of Flash and redirects to a compromised site.
- An iframe on the compromised site redirects to Sundown EK.
- ai.rqrzq[.]com and dqg.rkrtk[.]com is Sundown EK, from top to bottom -> Landing Page -> Flash -> Payload
- Dropped payload “z3qpfzic.exe”.
-
SHA256: 43e30e3a58772743ad3fa4ae75de1a06204219eb80fbfc53fdb884d830942d44 File name: z3qpfzic.exe Detection ratio: 6 / 58 - Known also as Terdot A, Zloader periodically sends data to a command and control.
- Interestingly I had some ET signatures for exploits used by White Lotus EK:
- ET CURRENT_EVENTS Possible WhiteLotus EK 2013-2551 Exploit 3 (A Network Trojan was Detected) [2017738]
ET CURRENT_EVENTS Possible WhiteLotus EK 2013-2551 Exploit 2 (A Network Trojan was Detected) [2017737]
ET CURRENT_EVENTS Possible WhiteLotus EK 2013-2551 Exploit 1 (A Network Trojan was Detected) [2017736]