Summary:
My last source of Terror appeared to dry up and other security researchers such as @jeromesegura have reported changes in Terror EK. I initially looked at the referrers provided in the article and saw the same patterns.
However today I found a fresh Terror EK from malvertising and it appears to be “complete” in the sense that it now includes 4 Flash exploits (one of which had not been uploaded to VT for 5 months) and Silverlight exploit was not hosted on another domain. The only thing Terror EK has not done is a proper obfuscation of its code but I guess these are well known exploits and there is no requirement.
Overall it is clear Terror EK is in development by whomever controls it now. This version appears to look more like a main stream EK. All it needs is some strong obfuscation to slow down researchers especially if a new exploit is discovered.
Background Information:
- An article on Terror exploit kit showing changes in the patterns:
- Some Exploits used by this version of Terror EK:
http://malware.dontneedcoffee.com/2013/11/cve-2013-0074-silverlight-integrates.html
http://malware.dontneedcoffee.com/2014/11/cve-2014-6332.html
http://malware.dontneedcoffee.com/2013/11/cve-2013-2551-and-exploit-kits.html
Downloads (in password protected zip)
- 130417-TerrorSmokePcap– PCAP.
- 140417TerrorSmokePayload– Flash, Silverlight and Smoke Loader
Notable Details:
- Payload was zoskoezb.exe-> VirusTotal (4cd37ab66af60b7a709c3b17fb3692ae784b3897e442f7bff4a9374ea5719110)
- I had left Smoke Loader running creating a mess of a PCAP so here is the Hybrid Analysis Report – Here
Malvertising Chain
Terror EK – (185.82.202.40)
Details of infection chain:
(click to enlarge!)
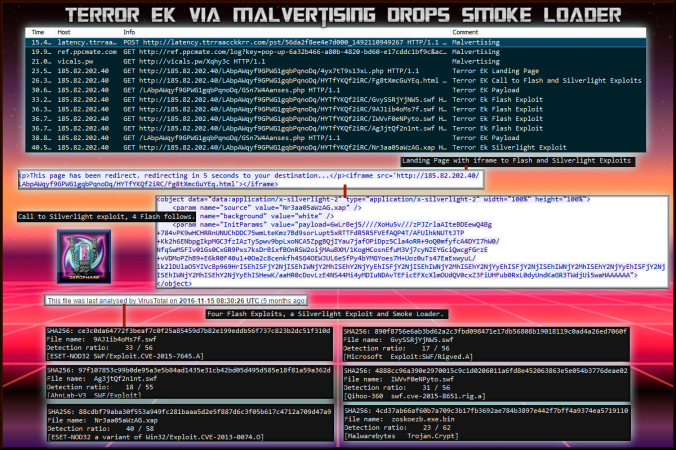
Terror EK using 4 Flash Exploits and Silverlight as well as the usual IE exploits drops Smoke Loader.
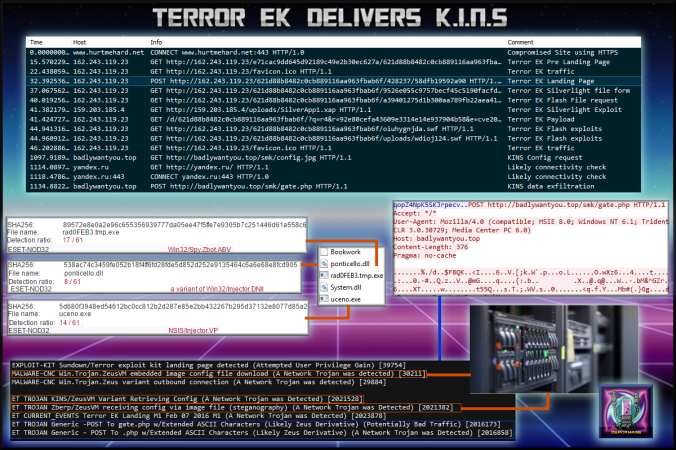
For comparison here was my last Terror EK detection:
- Post infection was Smoke Loader. It downloaded a variety of malwares but I have not included this in the PCAP. The samples however I have uploaded here.
Full Details:
- The landing page contains a single iframe that loads multiple Flash exploits and a Silverlight. This has changed from multiple iframes. After this comes the usual landing page exploits. Nothing appeared to be obfuscated beyond some URL encoding. At the end of the script is a call to the payload.


- The iframe from the landing page redirects to a page that contains 4 Flash exploits and one Silverlight. One of the Flash exploits had not been uploaded to VT in 5 months.

Here are the VirusTotal reports note 9AJ1ib4oMs7f.swf is the “newer” Flash exploit:
| SHA256: | 4cd37ab66af60b7a709c3b17fb3692ae784b3897e442f7bff4a9374ea5719110 |
| File name: | zoskoezb.exe.bin |
| Detection ratio: | 23 / 62 |
| SHA256: | 88cdbf79aba30f553a949fc281baaa5d2e5f887d6c3f05b617c4712a709d47a9 |
| File name: | Nr3aa05aWzAG.xap |
| Detection ratio: | 40 / 58 |
| SHA256: | 4888cc96a390e2970015c9c1d0206011a6fd8e452063863e5e054b3776deae02 |
| File name: | IWVvF0eNPyto.swf |
| Detection ratio: | 31 / 56 |
| SHA256: | 890f8756e6ab3bd62a2c3fbd098471e17db56808b19018119c0ad4a26ed7060f |
| File name: | GvySSRjYjNW5.swf |
| Detection ratio: | 17 / 56 |
| SHA256: | 97f107853c99b0de95a3e5b84ad1435e31cb42bd05d495d585e18f81a59a362d |
| File name: | Ag3jtQf2n1nt.swf |
| Detection ratio: | 18 / 55 |
| SHA256: | ce3c0da64772f3beaf7c0f25a85459d7b82e199eddb56f737c823b2dc51f310d |
| File name: | 9AJ1ib4oMs7f.swf |
| Detection ratio: | 33 / 56 |




Pingback: Finding a Good Man: Part 2 – MALWARE BREAKDOWN