Summary:
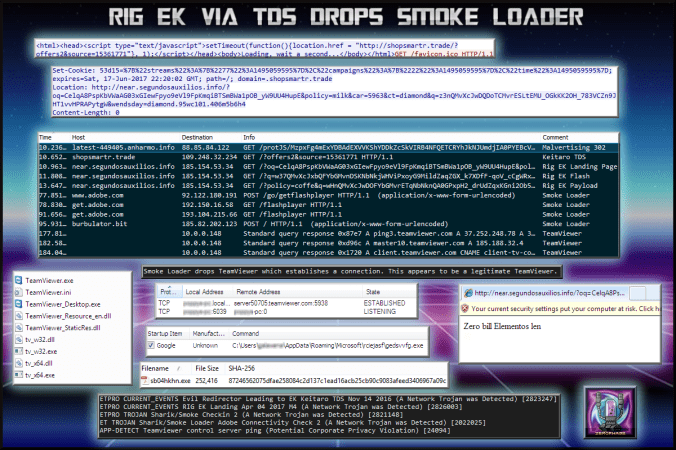
This decoy site was serving Philadelphia ransomware the day before. I found it again through a malvertising chain and now believe it was served by Keitaro TDS.
This time it dropped Smoke Loader which downloaded and installed TeamViewer. This appeared to be a legitimate version or at least it did not trigger any AV alerts on VirusTotal. I saw an established connection but did not notice anything odd with my host. Unlike other times I have seen Smoke Loader, there was only this payload.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- In depth look at Smoke Loader:
Downloads
(in password protected zip: (infected))
- 18-May-2017-Rig-Smoke -> Pcap
- 18-May-2017-Rig-Smoke-CSV -> CSV of the traffic for IOC’s
- 18-May-2017-Smoke-TeamViewer -> Smoke Loader and TeamViewer
Details of infection chain:
(click to enlarge!)
Full Details:
A malvertising chain (possible Keitaro TDS) leads to a 302 to Rig EK.
The Rig Landing Page is hosted on IP 185.154.53.34. The landing page displayed the text “Zero bill Elementos len” in the browser.
The payload dropped was Smoke Loader which among the usual Adobe checkin requests, made a request to ” burbulator.bit” which returned config. TeamViewer was installed which appeared to be a legitimate version :
| SHA256: | 96578ec1817e9a5144cfa427b6c9aa6c14dd42b08d9d51fe1e2a98281024632e |
| File name: | TeamViewer.exe |
| Detection ratio: | 0 / 61 |
The file established connection to TeamViewer servers though I did not see anyone messing about on my host. I left it running for around an hour and nothing else was dropped by SmokeLoader.


Pingback: Rig EK Drops Bunitu, Smoke Loader, Andromeda and a Miner | Zerophage Malware