Summary:
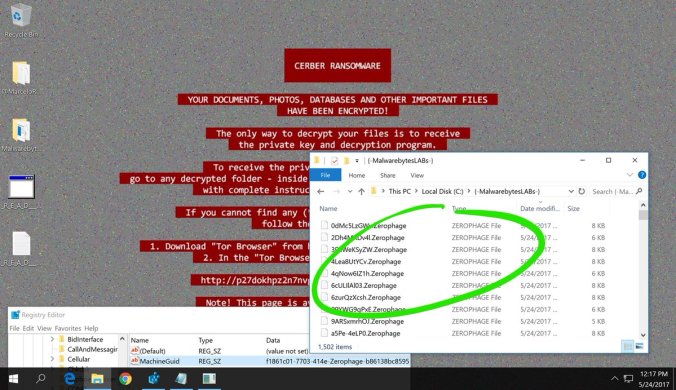
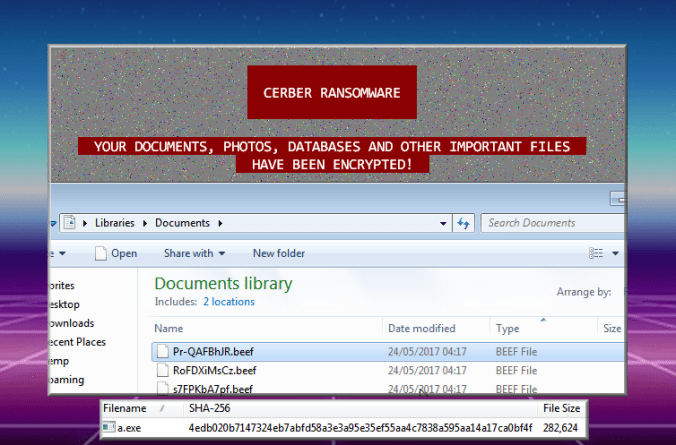
Magnitude EK still continues to drop Cerber ransomware. In this flow Magnitude EK has renamed its scriplet from .sct to a .ico file. Cerber encrypted all files with a .BEEF extension in this instance. All this occurred within 60 seconds of visiting the malvertising chain. This was likely sped up by my new VM which is 64 bit and has more horse power.
I like to track Magnitude even though it’s range is very limited, it still appears to be updating and I’m fairly sure if any browser exploits are released from the June Shadow Brokers that the Magnitude threat actors will jump on those in a flash.
Background Information:
- Article from RSA, although a few months old and missing some newer aspects of Magnitude, the fundamentals have not changed.
- Previous Magnitude EK posts from me.
Multiple Magnitude EK drops Cerber Ransomware Samples
Downloads (in password protected zip)
- 24-May-2017-Magnitude-Cerber– PCAP of Magnitude and Cerber
- 24-May-2017-Cerber– Cerber (a.exe – 4edb020b7147324eb7abfd58a3e3a95e35ef55aa4c7838a595aa14a17ca0bf4f)
- 24-May-2017-Magnitude-Cerber-CSV – CSV of traffic with resolved IP addresses.
Details of infection chain:
(click to enlarge!)
Full Details:
This flow was found through a malvertising chain. A series of 302 redirects leads to the first Magnitude profiling gate on a compromised website. These website are usually hosting financial scams. If you do not pass the profiling you are presented with a normal looking website.
I have detailed Magnitude EK in previous posts so please refer to the “background information” section above for more info.
I have changed my VM recently to a 64 bit machine. I also made a few changes to make Magnitude EK less noisy. In this run it took around 60 seconds to become infected with Cerber and no pesky UAC alerts came up.
Below is Magnitude EK’s Flash file and the payload “a.exe” which was Cerber.
| SHA256: | e927fff8fe693e9c92fdbc51aeb2714a4d12aa41c6105db7e245ce9f15aa38a9 |
| File name: | gwssy.swf |
| Detection ratio: | 0 / 55 |
| SHA256: | 4edb020b7147324eb7abfd58a3e3a95e35ef55aa4c7838a595aa14a17ca0bf4f |
| File name: | a.exe |
| Detection ratio: | 23 / 59 |
Cerber Encrypted my files with a .BEEF extension. I tweeted this earlier and discovered (thanks to@MarceloRivero in fact Cerber encrypts with a random 4 character extension based on the machine GUID.)
https://twitter.com/MarceloRivero/status/867415217034211329
In addition Magnitude EK has changed it’s scriptlet to a .ico instead of a .sct extension. This scriplet is used to bypass Applocker however the payload failed to run.
ETPRO TROJAN App Whitelist Bypass Via Com Scriptlet Inbound (A Network Trojan was Detected) [2819903]
Here is a deobfuscated version revealing what it does:



Pingback: Magnitude EK drops “CBRB” (Cerber Ransomware) | Zerophage Malware
Pingback: Magnitude EK drops Cerber (Scriplet changed to “.bmp”) | Zerophage Malware