Summary:
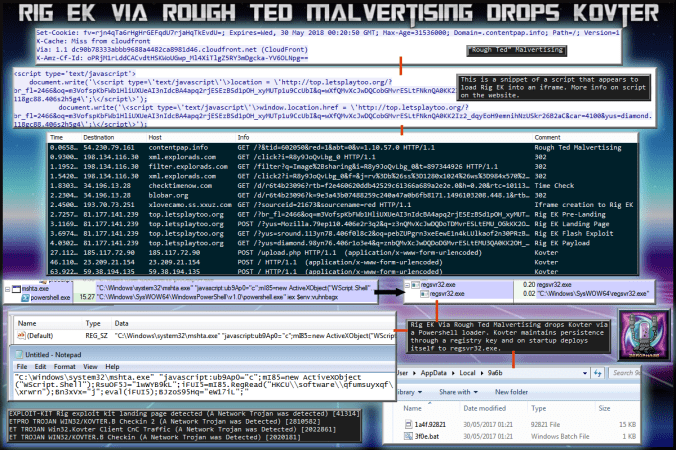
I stumbled across an article by MalwareBytes regarding a “new” malvertising campaign they had called “RoughTed” on account of the first domain they discovered. I have not seen anyone report Rig EK publicly at least not Twitter from this campaign. Apparently it is almost a year old.
Anyway I attempted several runs and eventually landed on Rig EK which dropped Kovter click-fraud malware. Initially I did not know what this malware was having never seen it so I requested the aid of @Antelox who identified it but also noted that it was loaded by a PowerShell script which was unusual for Kovter.
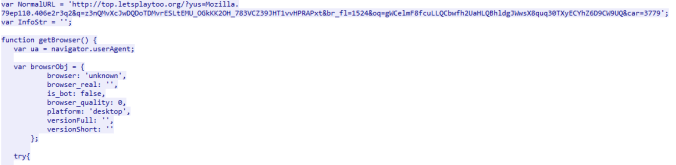
The iframe to Rig EK is interesting, almost unnecessarily large script that likely does other things. Pour over the PCAP/CSV and HA report for IOC’s.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on Rough Ted:
https://blog.malwarebytes.com/cybercrime/2017/05/roughted-the-anti-ad-blocker-malvertiser/
- Article on Kovter:
https://blog.malwarebytes.com/threat-analysis/2016/07/untangling-kovter/
Downloads
(in password protected zip: (infected))
- 30-May-2017-Rig-Kovter-PCAP -> Pcap
- 30-May-2017-Rig-Kovter-CSV -> CSV of the traffic for IOC’s
- 30-May-2017-Kovter-> Kovter
- Link to Hybrid Analysis for extra IOC’s -> Here
Details of infection chain:
(click to enlarge!)
Full Details:
RoughTed is a malvertising operation known for it’s wide scope. See the MalwareBytes article above for a more in depth dive. In this chain I started with the RoughTed URL and within 5 second Rig EK had dropped a payload.
A series of 302 redirects and a check for time and possibly geo ip finally led to a domain that contained a script that appears to load Rig EK into an iframe.
Rig EK contained a pre-landing page which makes several environment checks before initiating a POST request to the landing page.
Rig Dropped Kovter – a click fraud malware known for its persistence techniques.
| SHA256: | 9674fe85726c33f982d58eb362cd598cd944dd8f3f9d0a1b5506b9470cb4b57e |
| File name: | muabump0.exe |
| Detection ratio: | 20 / 59 |
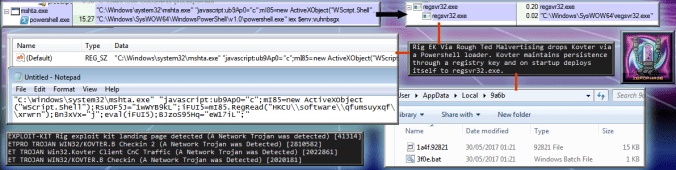
Although the malware ran fine on my machine, i did sumbit it to Hybrid Analysis to identify all IOC’s. I missed the loader part which was identified by @Antelox when I gave him the sample to identify. Kovter appeared to be loaded by a huge powershell script. The image below is at max zoom and is only a 1/3rd of the script.
Below is the bottom half the the infographic which shows Kovter’s persistence.
It is described in great detail by MalwareBytes. I used the article to match IOC’s.



Pingback: Magnitude EK via RoughTed drops Cerber Ransomware | Zerophage Malware