Summary:
Here I have four Rig EK flows from 13-16 June from malvertising chains. The payloads were Chthonic and Bunitu. I have not gone into much detail in this blog regarding the infection chains as I have already written about them in previous blogs. These however are all new referrers which may be worth noting.
There are 3 gates here to redirect to Rig:
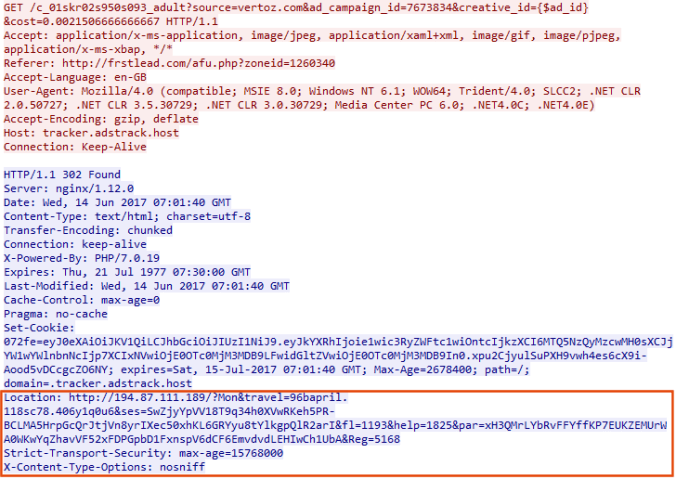
- A simple 302 redirect
- Bunitu’s “Small Gate”
- At least two domains with the same pattern “IndexZ Gate”
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Oldish article regarding Chthonic banking trojan:
https://securelist.com/blog/virus-watch/68176/chthonic-a-new-modification-of-zeus/
- Article on Bunitu Trojan:
https://blog.malwarebytes.com/threat-analysis/2015/07/revisiting-the-bunitu-trojan/
Downloads
(in password protected zip: (infected))
- 16-June-17-MultiRig-PCAP -> Pcaps of traffic
- 16-June-17-MultiRig-CSV -> CSV of the traffic for IOC’s
- 16-June-2017-Chthonic-Bunitu -> ZeuS Chthonic and Bunitu
Details of infection chain:
(click to enlarge!)
Full Details:
All flows were found through malvertising chains between 13-16 June 2017. Below are two previous blogs that cover Chthonic and Bunitu.
Due to time issues I was unable to capture all the activity from my lab. Instead with the assistance of @LedTech3 i was able to recover the payloads from the PCAP’s. I have ran them through Hybrid Analysis
advert-mal.bin (Chthonic)
SHA256 – 159cda8598b1916bcdeba8c31b88183e576d49673da6635c26f36ff9c291de07
C2 – HTTP – POST – pationare.bit/ – 86.110.117.53 POST – pationare.bit/www/ – 86.110.117.53
jackportreroll-mal.bin (Bunitu)
SHA256 – 61982aa119f5297d23300d59a1f7bcc030348025d8a224ca50894652d815a42b
C2 – DNS – p.onlinecbbeer.com – 84.210.101.33
DNS – f.onlinecbbeer.com – 94.106.242.28
shoppinwithus-mal.bin (Chthonic)
SHA256 – afc31940380359380f27cd0cbcc18f9eb67027107d434d190a725f124b1b554e
C2 – HTTP – POST – letit2.bit/home/www/ – 47.91.124.165 POST – letit2.bit/www/ – 47.91.124.165
youcaught-mal.bin (Chthonic)
SHA256 – 4a96c45844fa6719b91d525c97b9cad479c92eec44c16f969ce7f3a3aa1a99c1
C2 – HTTP – POST – letit2.bit/home/www/ – 47.91.124.165 POST – letit2.bit/www/ – 47.91.124.165