Summary:
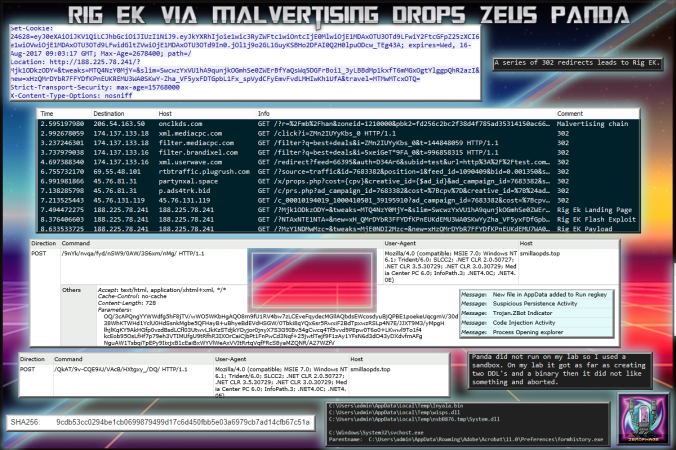
Today I found Panda Banker via a series of 302 redirects to Rig EK. The payload did not run on my lab so I sought the aid of @Antelox who identified it as Panda. I then put the sample into a sandbox where it did run so I managed to pull a few IOC’s.
It has been a while since I’ve seen Panda Banker I’ll have to pour over the data and figure out why it evaded my lab but ran in a sandbox..
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on Panda Banker
https://cyber.wtf/2017/02/03/zeus-panda-webinjects-a-case-study/
Downloads
(in password protected zip)
- 16-July-2017-Rig-Panda-PCAP -> Pcap
- 16-July-2017-Rig-Panda-CSV -> CSV of traffic for IOC’s
- 16-July-2017-Rig-Malware -> Panda (9cdb53cc0294be1cb0699879499d17c6d450fbb5e03a6979cb7ad14cfb67c51a)
Details of infection chain:
(click to enlarge!)
Full Details:
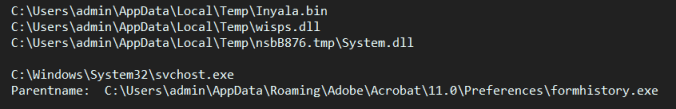
Found via a malvertising chain of multiple 302 redirects, Rig EK drops Panda Banker. The sample did not run on my lab. It created three files then terminated. It must have checked for something and disliked it then terminated. The sample was confirmed to be Panda by @Antelox.
| SHA256: | 9cdb53cc0294be1cb0699879499d17c6d450fbb5e03a6979cb7ad14cfb67c51a |
| File name: | 16-July-2017-Rig-Malware.bin |
| Detection ratio: | 19 / 63 |
| Avira (no cloud) | TR/AD.PandaBanker.fyxdz |
Although it did not run, I did managed to put it into a sandbox which managed to run it so I have some IOC’s for traffic.
The PCAP is located here: https://www.virustotal.com/en/file/7ebd871771bfaa3eb6d3f4ffd638d709a251fd4fa487dfe0c2a9f58a7374e21c/analysis/
On my lab it created the three files below but then terminated. On the sandbox it copied itself to the path below and did the usual trojan behaviour (process injection, etc.)
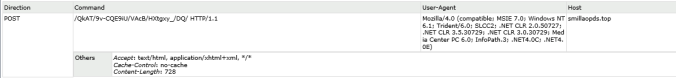
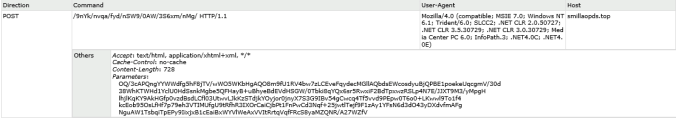
Below is port 443 HTTP POST requests which were observed to smillaopds.top.
There was a lot more data but I’ll end with a quick summary that the sandbox gave: