Summary:
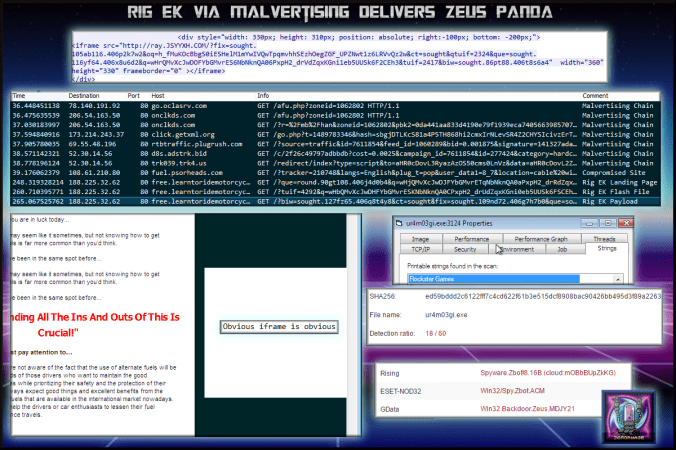
I’ve been looking at this compromised site for a days now. It had previous dropped Chthonic ZeuS variant and other times no payload at all. The iframe that contains the redirect is not hidden. On one occasion it failed to connect to Rig EK which was displayed as an error within the iframe.
This time the payload was Panda ZeuS variant. It would not run properly in my VM or online sandboxes. So once again I sought the help of @Antelox who quickly identified it as ZeuS variant Panda banker. Looks like I’ll have to try to harden my environment a bit as it appears to have evasive capabilitiies
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- In depth look at web injects from Panda:
https://cyber.wtf/2017/02/03/zeus-panda-webinjects-a-case-study/
Downloads
- Rig170217-> Pcap and exe in password protected zip.
Notable Details:
- 78.140.191.92 – go.oclasrv.com – Starting Ad Server
- Multiple 302 redirects lead to compromised site
- 108.61.210.80 – fuel.psorheads.com – Compromised Site
- 188.225.32.62 – free.learntoridemotorcycle.com – Rig EK
- Payload was ur4m03gi.exe-> VirusTotal
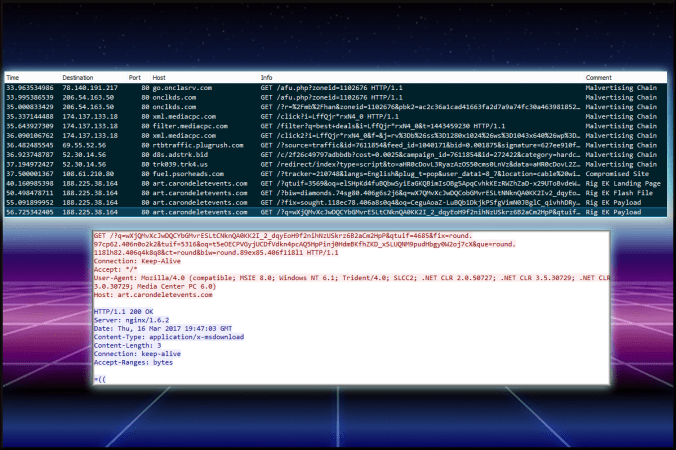
- Failed run from a few days ago:
- 78.140.191.217 – go.onclasrv.com – Starting Ad Server
- Multiple 302 redirects lead to compromised site
- 108.61.210.80 – fuel.psorheads.com – Compromised Site
- 188.225.38.164 – art.carondeletevents.com – Rig EK
Details of infection chain:
(click to enlarge!)
Full Details:
- A malvertising chain used multiple 302 redirects.
- iframe to Rig EK on the compromised website
- free.learntoridemotorcycle.com -> Landing Page -> Flash -> Payload
- Dropped payload “ur4m03gi.exe”
-
SHA256: ed59bddd2c6122fff7c4cd622f61b3e515dcf8908bac90426bb495d3f89a2263 File name: ur4m03gi.exe Detection ratio: 18 / 60 - This was identified as Panda which is a ZeuS variant by @Antelox.
- The payload ran for around 30 seconds before creating a .bat file which it executed in order to delete itself.
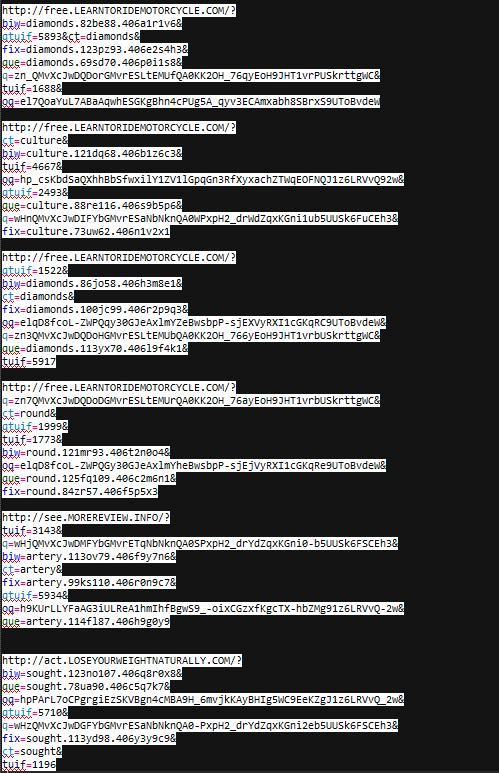
- Below are some additional Rig EK landing page URL’s.
- The parameters “qtuif”, “fix” and “que” are very new additions however spot the pattern in the “q” parameter which has not changed 🙂
Pingback: Rig EK via Malvertising drops Panda Banker | Zerophage Malware