Summary:
Its been a fairly standard week for Rig EK. I’ve not spotted anything new or interesting so I decided not to blog about it this week. I did however discover a change in Magnitude EK. It’s a small one but the Scriplet now has the extension “.bmp” instead of “.ico”.
I also ran this flow with the latest IE 11 and Flash Player and still got Cerber Ransomware (still calling itself CRBR). If you’ve ever fiddled with security settings you’ll probably scream that scriplets are disabled by default which is true. I did play with the security settings to try to give see what payload the scriplet drops. Alas they still failed as usual and Cerber appeared from it’s normal vector.
Background Information:
- Article from RSA, although a few months old and missing some newer aspects of Magnitude, the fundamentals have not changed.
- A few previous Magnitude EK posts from me.
Multiple Magnitude EK drops Cerber Ransomware Samples
Magnitude EK drops “CBRB” (Cerber Ransomware)
Magnitude EK via malvertising delivers Cerber Ransomware
Downloads (in password protected zip)
- 03-July-2017-Magnitude-Cerber-PCAP– PCAP of Magnitude and Cerber
- 03-July-2017-Cerber– Cerber (a.exe – 46e29c56d426a4c16548b74f77b2fdd75005ddac1333039567d16212cdc585e4)
- 03-July-Magnitude-Cerber-CSV – CSV of traffic with resolved IP addresses.
Most notable about this flow is the change of the naming of the scriplet used by Magnitude EK.
The scriplet is called in the landing page. I have deobfuscated most of it and you can see the call to the “.bmp” scriplet. Previous it has been “.ico”.
This is the scriplet mostly deobfuscated with some variables renamed. Here you can see an executable is dropped and ran with cmd. These executables always fail and are 0 kb. I’m not sure why this is the case.
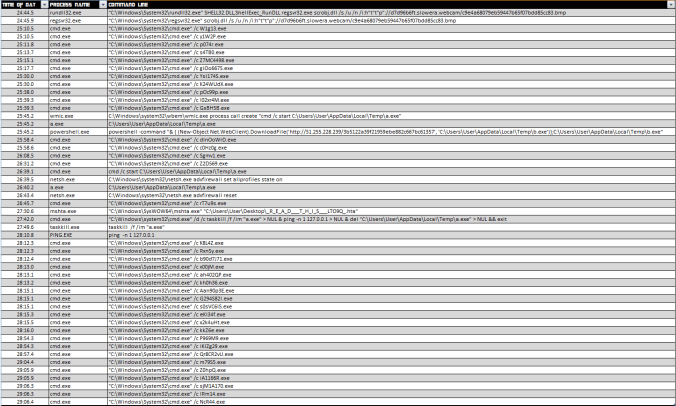
If you enlarge this picture you will see a condensed version of all the processes that were run on the endpoint.
The payload is Cerber Ransomware. This version calls itself “CBRB”.
This version of a Cerber is at least a week old (UDP patterns are identical but sample is fresh from 3rd) however it still does a good job at evading a lot of AV vendors.
| SHA256: | 46e29c56d426a4c16548b74f77b2fdd75005ddac1333039567d16212cdc585e4 |
| File name: | a.exe |
| Detection ratio: | 14 / 61 |





Pingback: Magnitude EK XML Package and changes. | Zerophage Malware