Overview
I received this email on several email accounts. You can read about more specific details on Dynamoo’s Blog which is a great site for malspam. This is my first attempt at reporting on malspam it in this manner.
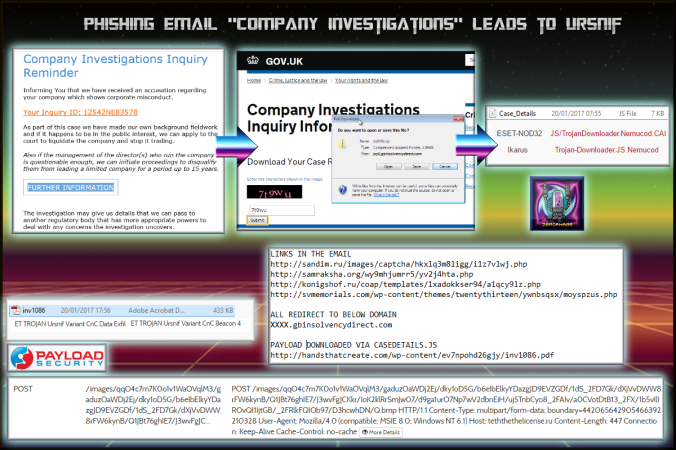
My sample was slightly different. Different domains and when I ran it through Hybrid Analysis there was a POST request which triggered the signature “ET TROJAN Ursnif Variant CnC Data Exfil”. There is some indication that it could be ransomware (Cerber or Nemucod) but the POST request does not match either of these. I was unable to run the sample in my lab (although i did do it in another lab) so unfortunately no PCAP is available.
In short the link in the email redirects to a domain that appears to be from the UK government and is fairly convincing. There a CAPTCHA code required to download the file and you do actually have to input the correct code. This downloads a ZIP and in the ZIP is a JS file called “Case Details.js”. When executed this script downloads a “PDF” which is actually an executable.
Downloads
zeroursnifmalspa – This ZIP contains the JS downloader and the “PDF” in a password protected ZIP.
Notable Details:
- 35.166.113.223 -> XXXX.gbinsolvencydirect[.]com -> All initial links redirect to this domain (random subdomain).
- 104.238.71.250 -> http://handsthatcreate[.]com/wp-content/ev7npohd26gjy/inv1086[.]pdf -> Payload from the JS downloader
- 213.111.163.37 -> POST /images/qqO4c7m7K0o1v1WaOVqlM3/gaduzOaWDj2Ej/dky1oD5G/b6eIbElkyYDazgJD9EVZGDf/1dS_2FD7Gk/dXjVvDWW8rFW6kynB/Q1JBt76ghIE7/J3wvFgJCKkr/IoK2klRrS mJw07/d9ga1urO7Np7wV2dbnEiH/uj5TnbCyo8_2FAIv/a0CVotDtB13_2FX/1b5vIlIROvQI1IjtGB/_2FRlkFQIOb97/D3hcwhDN/Q.bmp -> Ursnif CnC
Details of infection chain:
Further Details:
-
SHA256: 8d2bd198ca268762b9e429f44c68f8953e1dce60bc1bc820ff82c87ebd3e4eb6 File name: Case_Details.js Detection ratio: 7 / 53 -
SHA256: 98c939c7a2406055ad0c000c6c27b46a2cba29eaf5f8a9eafd93c8bf573f309b File name: inv1086.pdf Detection ratio: 30 / 55
- Result of inv1086.pdf on Hybrid Analysis which shows Urnsif CnC.