Summary:
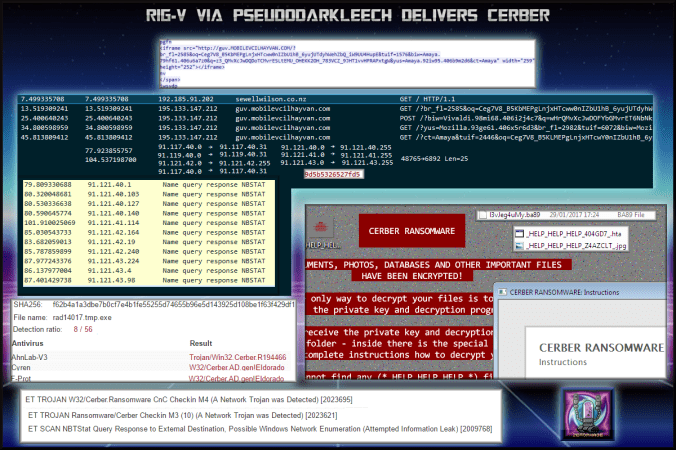
I finally sorted out my lab and successful got Cerber infection which encrypted everything with a .ba89 extension. Interestingly this Cerber did not send the standard HTTP request you would expect from Cerber. I did see a lot of Nbstat responses however from several of the IP addresses that sent data over UDP port 6892. I’m presuming these responses is what has allowed Cerber proceed with encryption.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on the PseudoDarkleech campaign and its history:
http://researchcenter.paloaltonetworks.com/2016/12/unit42-campaign-evolution-pseudo-darkleech-2016/
Downloads
- 300117-rigcerber -> Contains pcapng and payload in password protected zip.
Notable Details:
- 192.185.91.202 – sewellwilson.co[.]nz – COMPROMISED WEBSITE
- 195.133.147.212 – guv.mobilevcilhayvan[.]com – RIG-V
- 91.117.40.0 -> 91.117.40.31 UDP port 6892 – Cerber Check In IP Range
- 91.119.40.0 -> 91.119.40.31 – UDP port 6892 – Cerber Check In IP Range
- 91.121.40.0 -> 91.121.40.255 – UDP port 6892 – Cerber Check In IP Range
- 91.121.41.0 -> 91.121.41.255 – UDP port 6892 – Cerber Check In IP Range
- 91.121.42.0 -> 91.121.42.255 – UDP port 6892 – Cerber Check In IP Range
- 91.121.43.0 -> 91.121.43.255 – UDP port 6892 – Cerber Check In IP Range
- Payload was rad14017.tmp.exe -> VirusTotal
- I also put it into HybridAnalysis which failed to deliver Cerber indicating that Cerber might be able to detect a sand boxed environment.
- Created several additional files.
Details of infection chain:
Full Details:
- Compromised site redirects to Rig-V EK via PseudoDarkleech iframe.
- guv.mobilevcilhayvan[.]com is Rig EK, from top to bottom -> Pre-Landing -> Landing Page -> Flash -> Payload
- UDP traffic port 6892 all contained the data”9d5b5326527fd5“
- Dropped payload “rad14017.tmp.exe “.
-
SHA256: f62b4a1a3dbe7b0cf7e4b1fe55255d74655b96e5d143925d108be1f63f429df1 File name: rad14017.tmp.exe Detection ratio: 8 / 56 - Payload encrypted files with a “.ba89” extension.
- I did not see the usual HTTP request of Cerber. It is likely the Nbstat responses are giving Cerber the go ahead.
- Emerging Threat signatures for Cerber and NBTStat query response.
- Even though I see the Conficker emerging threat signature I can now safely rule this out.
- Cerber changes the background and loads a HTA file containing instructions on how to decrypt your files. It also plays an eerie audio stating that your files have been encrypted in the Windows 7 female USA voice.