Summary:
Over the past few days I’ve been looking at Cerber for any changes and trying to track Sundown. I have received information to believe that Sundown is no longer operational. Anyway I returned to my usual malvertising chain but I was unable to capture the traffic as accurately as before.
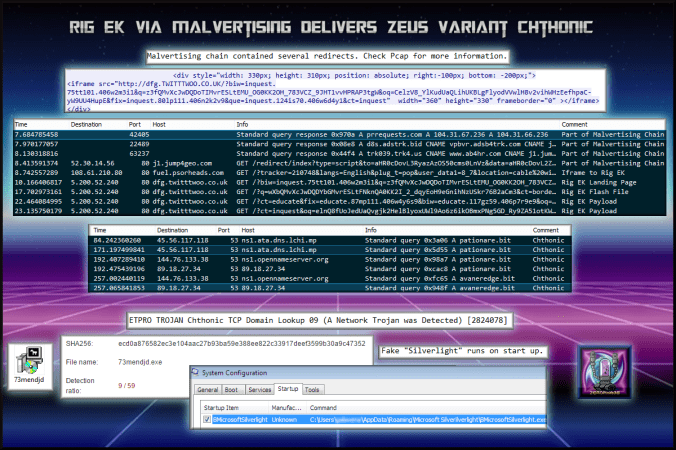
This time the payload was Chthonic which is a ZeuS variant. At first I could not identify the sample so requested the help of @Antelox who quickly identified it. Upon further investigation I noticed the DNS requests which I recognised from reading MalwareTraffic in the past. I then checked my ET signatures and found one for Chthonic.
Always good to see different variants of malware and from other sources other than PseudoDarkleech and EITest.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Oldish article regarding Chthonic banking trojan:
https://securelist.com/blog/virus-watch/68176/chthonic-a-new-modification-of-zeus/
Downloads
- rigchthonicPCAP -> Pcap in password protected zip. (2nd pcap has CnC traffic)
- 130317rigchthonic-> Payload (Chthonic) in password protected zip. Unfortunately I have to use File Dropper, having a few issues with getting this file on my site.
Notable Details:
- Multiple 302 redirects lead to compromised site
- 108.61.210.80 – fuel.psorheads.com – Compromised Site
- 5.200.52.240 – dfg.twitttwoo.co.uk – Rig EK
- 45.56.117.118 – pationare.bit – Chthonic Domain Lookup
- 144.76.133.38 – pationare.bit – Chthonic Domain Lookup
- 89.18.27.34 – pationare.bit – Chthonic Domain Lookup
- 144.76.133.38 – avaneredge.bit – Chthonic Domain Lookup
- 89.18.27.34 – avaneredge.bit – Chthonic Domain Lookup
- Payload was 73mendjd.exe -> VirusTotal
Details of infection chain:
(click to enlarge!)
Full Details:
- A malvertising chain used multiple 302 redirects. I had some issue capturing all the traffic so it is not all listed in the image above.
- iframe to Rig EK on the compromised website
- dfg.twitttwoo.co.uk -> Landing Page -> Flash -> Payload
- Also to note there are slight changes in Rig EK’s URL patterns. The parameters “fix” and “que” are present although not shown in the picture.
- Dropped payload “73mendjd.exe” which is different to the usual “rad” themed ones.
-
SHA256: ecd0a876582ec3e104aac27b93ba59e388ee822c33917deef3599b30a9c47352 File name: 73mendjd.exe Detection ratio: 9 / 59 - This was identified as Chthonic which is a ZeuS variant by @Antelox.
- Chthonic lay idle for some time in processes. It eventually created a fake Silverlight executable and deleted the original payload and forced a reboot.
- After reboot the malware had added a start up entry.
- No POST traffic was observed.