Summary:
After having found the previous Terror EK I went searching for it again a few days later. I found what I initially thought was Terror EK but did not get any ET signatures for the landing page. I then saw it did not appear to resemble my last analysis as in there were no Flash exploits. Instead there was a SilverLight exploit.
I decided to tweet it out to the wider community of a few EK hunters I know:
https://twitter.com/Zerophage1337/status/847225885610491905
It was confirmed by all to be Terror EK. Infact I had missed a Snort rule which said it was Terror EK. Often Snort rules don’t seem to pick up landing pages so I had thought not to look there. I shall from now on! Several people got involved so many thanks to them especially for identifying the payload.
For this sample I dug a bit further into the landing page code which you can see later on.
Background Information:
- An article on Terror exploit kit and my previous detection for comparison:
https://www.trustwave.com/Resources/SpiderLabs-Blog/Terror-Exploit-Kit–More-like-Error-Exploit-Kit/
https://zerophagemalware.com/2017/03/24/terror-ek-delivers-tofsee-spambot/
- Article about Terror EK dropping coin miner:
- Exploits used by this version of Terror EK:
http://malware.dontneedcoffee.com/2013/11/cve-2013-0074-silverlight-integrates.html
http://malware.dontneedcoffee.com/2014/11/cve-2014-6332.html
http://malware.dontneedcoffee.com/2013/11/cve-2013-2551-and-exploit-kits.html
Downloads (in password protected zip)
- PCAP-290317-TerrorEK – PCAP
- Coin Miner – Payload
Notable Details:
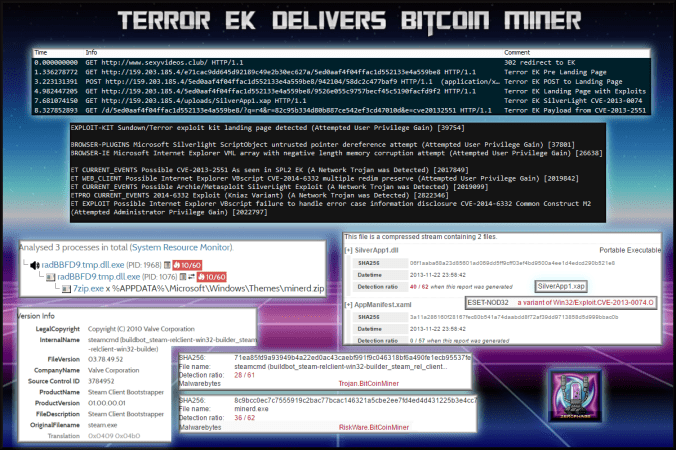
- 173.208.245.114 – sexyvideos.club – 302 redirect
- 159.203.185.4 – Terror EK traffic
- 69.65.17.35 – a.pomf.cat – Miner CnC (from Hybrid Analysis)
- Payload was rad5DA27.tmp.dll-> VirusTotal (71ea85fd9a93949b4a22ed0ac43caebf991f9c046318bf6a490fe1ecb95537fe
- It was submitted to Hybrid Analysis.
Details of infection chain:
(click to enlarge!)
Full Details:
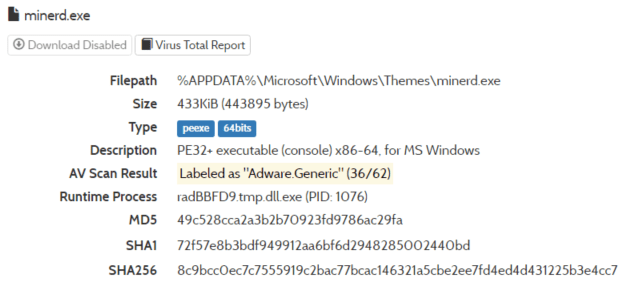
- The payload claims to be a Steam DLL.
- This payload was dropped however did not run on my environment. Possibly it did not meet the requirements.
| SHA256: | 71ea85fd9a93949b4a22ed0ac43caebf991f9c046318bf6a490fe1ecb95537fe |
| File name: | rad5DA27.tmp.dll |
| Detection ratio: | 6 / 61 |
- This is the final executable after being unzipped.
| SHA256: | 8c9bcc0ec7c7555919c2bac77bcac146321a5cbe2ee7fd4ed4d431225b3e4cc7 |
| File name: | minerd.exe |
| Detection ratio: | 36 / 62 |
| ESET-NOD32 | a variant of Win64/BitCoinMiner.U potentially unsafe |
- The payload downloads a filed called “miner.zip” and uses 7zip is unzip it.
- This variant of Terror EK did not use any Flash exploits. It appeared to use 3 other exploits.
- The initial landing page seemed to contain tracking and adverts which could a sort of pre-landing page. I could not locate any exploits within it. It however creates a POST request to the “real” landing page where the exploits are contained.
- On the landing page is an iframe leading to a metasploit SilverLight exploit.
- This is CVE-2013-0074
| SHA256: | 88cdbf79aba30f553a949fc281baaa5d2e5f887d6c3f05b617c4712a709d47a9 |
| File name: | SilverApp1.xap |
| Detection ratio: | 39 / 58 |
| ESET-NOD32 | a variant of Win32/Exploit.CVE-2013-0074.O |
| SHA256: | 06f1aaba68a23d85601ad069dd5ff9cff03ef4bd9500a4ee1d4edcd290b521e8 |
| File name: | SilverApp1.dll |
| Detection ratio: | 41 / 62 |
| ESET-NOD32 | a variant of Win32/Exploit.CVE-2013-0074.O |
- This is part of CVE-2014-6332 AKA Godmode. Note the payload URL contains the CVE number.
- And finally CVE-2013-2551 which is exploit that compromised my endpoint if you look at the URL on the main picture.





Pingback: Terror EK delivers ZeuSVM/K.I.N.S. | Zerophage Malware