Summary:
On 2 March a site was tweeted by @St3f4nMZ to myself and two others which claimed to show different Sundown patterns. This actually turned out to be Nebula EK.
By the time I had noticed and gotten around to checking Nebula was gone and Rig EK seemed to have taken its place.
The payload this time looked very strange. It looked like an information stealer but did not trigger any ET signatures and I could not find similar patterns anywhere in the wild. I ended up tweeting @Antelox who said it was August Stealer. It seemed to be a very unusual payload and was very interesting to watch.
At the time having no idea what I didn’t really know what to look for. By the time it had been identified (today) I had already wiped the machine so could not investigate further. None the less this is an interesting find and I hope you enjoy it. Files and PCAP’s are below.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on August Stealer:
Downloads
- 040317-RigAugust-> Contains pcapng and payload in password protected zip.
Notable Details:
- 188.215.92.103 – hurtmehard.net – Compromised site
- 92.53.97.222 – 1rew.neighbourhoodreunion.com – Rig EK
- 91.226.10.138 – POST blog.ru/blog/gate – August Stealer CnC
- Payload was qvzyux09.exe -> VirusTotal
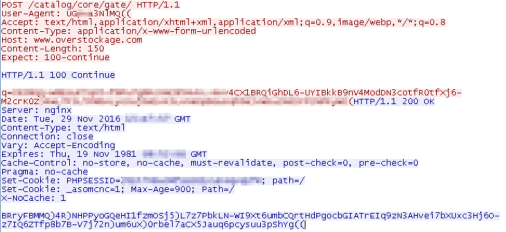
Details of infection chain:
(click to enlarge!)
Full Details:
- Compromised site has iframe redirecting to Rig EK.
- Site seemed to have two iframes which caused double landing page, etc.
- 1rew.neighbourhoodreunion.com -> Landing Page -> Flash -> Payload
- There was no Pre-Landing page.
- Dropped payload “qvzyux09.exe” which is different to the usual “rad” themed ones.
-
SHA256: de519cd2ac49e2d608f4785fb2434fbd0075e39ecfd482edab5b60524376cd12 File name: qvzyux09.exe Detection ratio: 29 / 59 - With the help of @Antelox this was identified as “August stealer”
- I used an article from Proofpoint to confirm that it was or at least this is a variant of August.
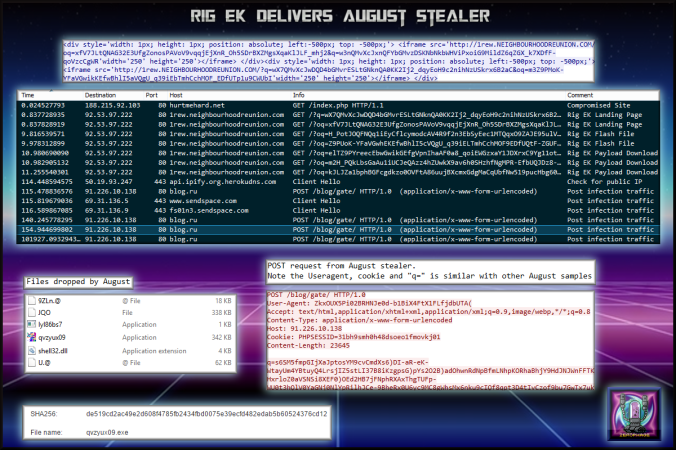
- This is a picture from Proofpoint of C2 traffic:
- Note the user agent, cookie and data after the “q=” is very similar to my POST traffic.
Pingback: Terror EK delivers ZeuSVM/K.I.N.S. | Zerophage Malware
Pingback: Finding a Good Man: Part 2 – MALWARE BREAKDOWN