Summary:
I have been following an IP over the past week which I originally found dropping an interesting coin miner. In attempt to find this miner again (as it appeared as if it was in dev) I began to look into it in more detail.
When a specific resource is targeted the browser is redirected to Rig EK or to a fake Flash file. All sites use the http.equiv attribute to refresh the screen loading Rig EK landing page URL. So far I have observed a coin miner, Chthonic and Zloader as payloads.
Unfortunately I had so many payloads and pcaps that I got lost within them and owing to a lack of time I have not been able to focus to prepare my usual style blog. None the less, this IP is a great source for Rig EK for those interested in studying it.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
Downloads
(in password protected zip: (infected))
- 11-June-2017-RigZloader -> Pcap
- 12-June-2017-Rig-Chthonic -> Pcap
Details of infection chain:
(click to enlarge!)
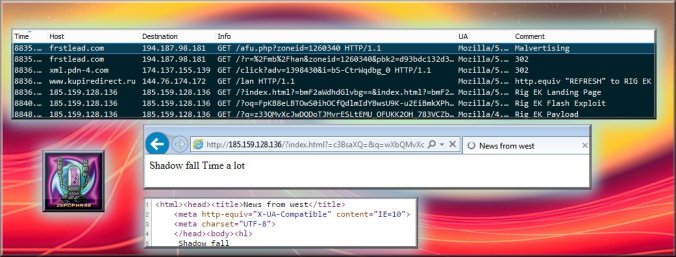
Rig EK displays “Shadow Fall”, drops Chthonic.
Full Details:
Lately I have been following an IP that is serving Rig EK via a http.equiv “REFRESH” attribute. This causes the page to refresh and “redirect” the browser to Rig EK.
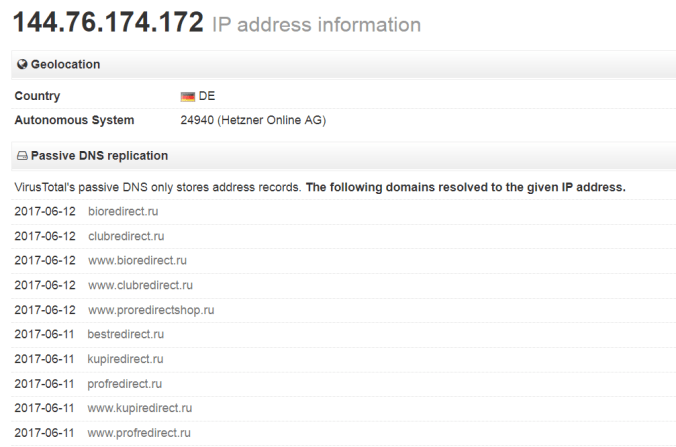
The IP (ASN 24940 (Hetzner Online AG) has several domains registered to it with a general theme of “XXXredirect.ru”
https://www.virustotal.com/en/ip-address/144.76.174.172/information/
Originally I found a domain hosted on this IP through RoughTed -> Rig EK via RoughTed drops a Miner
I have also found it through an “Onclkds” variant which is shown in the picture.
You can also just browse directly to one of these domains however you need to add a resource. So far I have seen three of these:
XXXredirct.ru/lan – Rig EK -> Chthonic
XXXredirct.ru/1 – Rig EK -> Zloader
XXXredirct.ru/xfile – Fake Flash -> Chthonic
There is a bit more information on the Flash file from the Twitter:
I also made a few tweets (and referenced in some) throughout the week in case you missed them:
And a bonus post of Bunitu and Magnitude: