Summary:
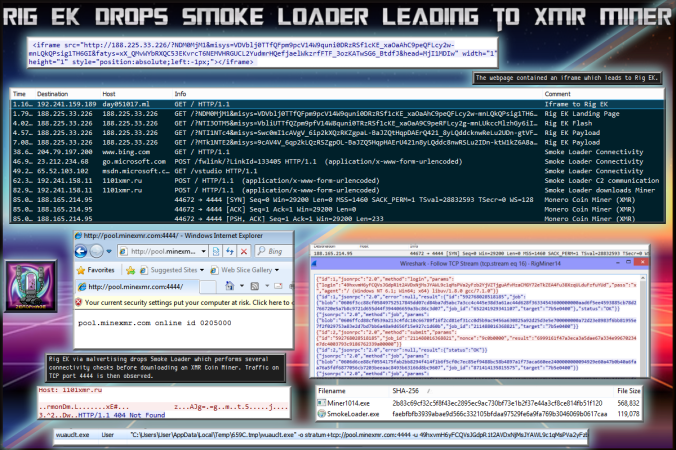
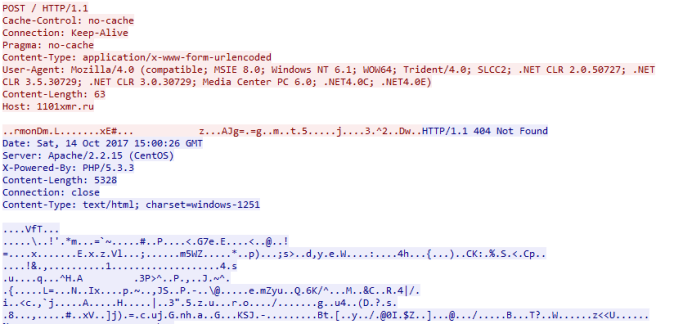
Yesterday I caught Rig EK dropping a variant of Smoke Loader which is different to todays one. Today’s sample is more consistent with what you would expect from Smoke Loader with its connectivity checks to popular domains like Microsoft and its attempts to hide processes. Yesterdays sample did not do any of this so campaign is likely ran by different threat actors.
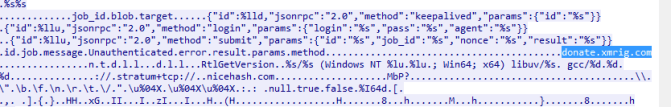
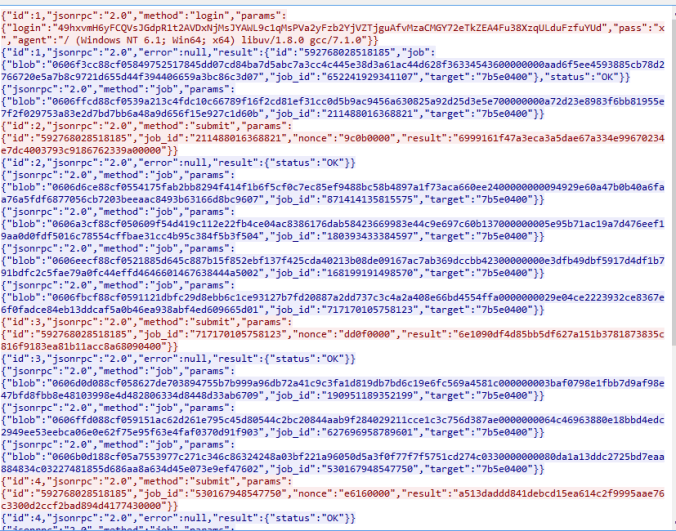
This time only an XMR miner was dropped which did begin to connect to the mining server on port 4444. No other payloads were witnessed. It’s worth keeping an eye on the IP of the domain that redirected to Rig EK as I’m sure it will be hosting different payloads later.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
Downloads
(in password protected zip)
- 14-October-2017-Rig-Smoke-PCAP-> Pcap of traffic
- 14-October-2017-Rig-Smoke-CSV-> CSV of traffic for IOC’s
- 14-October-2017-Rig-Smoke-> Smoke Loader – faebfbfb3939abae9d566c332105bfdaa97529fe6a9fa769b3046069b0617caa
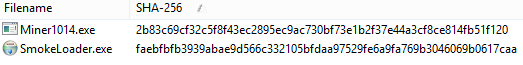
Smoke Loader- https://www.virustotal.com/#/file/faebfbfb3939abae9d566c332105bfdaa97529fe6a9fa769b3046069b0617caa/detection
XMR Miner – https://www.virustotal.com/#/file/2b83c69cf32c5f8f43ec2895ec9ac730bf73e1b2f37e44a3cf8ce814fb51f120/details
Details of infection chain:
(click to enlarge!)
Full Details:
The infection chain actually came from malvertising. The webpage contained a 1px iframe which leads to Rig EK.
![]()